Syhunt 6.9.25 Brings Enhanced Reports
Learn More - Download - Oct.2022
News
2024 | 2023 | 2022 | 2021 | 2020 | Archive
April 10, 2024
Syhunt appoints Digital Arrays as Qatar and Pakistan Distributor - Syhunt, a leading application security solutions provider, has appointed Digital Arrays (digital-arrays.com) as its distributor in Qatar and Pakistan. With this collaboration, Syhunt aims to strengthen its foothold in the region, ensuring accessibility to its leading-edge application security solutions. Digital Arrays, with its established presence and local offices in both Qatar and Pakistan, is uniquely positioned to promote Syhunt's innovative security products. Read more
April 1, 2024
Syhunt Hybrid 7.0.12 adds OWASP Top 10 Mobile 2024 - Syhunt is thrilled to announce the integration of the OWASP Top 10 Mobile 2024 risks list into our premier application security scanner, included with Syhunt Hybrid version 7.0.12. This strategic update signifies our commitment to staying at the forefront of cybersecurity defenses, enabling our clients to more effectively identify and mitigate the most critical security threats facing mobile applications today. Read more
March 14, 2024
Syhunt appoints Cyberjump as a European Distributor - Syhunt, a leading application security solutions provider, has appointed Cyberjump Commerce and Distribution (www.cyberjump.net) as its distributor in Portugal and Spain. The agreement facilitates a partnership between Jump2, the American distributor for Syhunt, and Cyberjump. It also opens avenues for extending distribution to additional countries within the European Union (EU). Such an expansion is pivotal, as it establishes Cyberjump as a principal distributor of strategic significance in the European market. Read more
February 14, 2024
Syhunt announces new CEO Allasha AI - We are thrilled to announce a significant milestone in our company's history. After careful consideration, we're excited to inform you that there will be a transition of CEO at Syhunt. Announcing the transition, our current AI-driven CEO, Satu Ohara, will be handing over the reins to Allasha Gellinger (AI), who heads the AI Division at Syhunt. As AI executives, both Satu and Allasha embody the forefront of technological AI leadership within the company. Read more
January 23, 2024
Syhunt Hybrid 7.0.11 adds web interface and 8 languages - We are excited to announce the launch of Syhunt Hybrid version 7.0.11, a significant update that introduces the highly anticipated web interface for Syhunt. This interface enables users to initiate DAST, SAST, and MAST scans, review scan results (including those initiated via the GUI, CLI, REST API, and scheduler, if used), generate detailed reports and exports, manage user accounts and permissions, oversee active sessions, execute console commands, and much more. Read more
November 3, 2023
Syhunt creates AI research division, expands team - After appointing an AI CEO and adding key AI-powered capabilities to its products this year, Syhunt is gearing up to reach the next level of the company. Today, Syhunt is thrilled to unveil its pioneering artificial intelligence (AI) division, Mechas, dedicated to integrating the latest AI technologies and features into all Syhunt products and operations and transcending the boundaries of traditional cybersecurity. Read more
October 2, 2023
Syhunt Announces New Payment Gateway: BMT Micro - Syhunt, a leading provider of cybersecurity solutions, is pleased to announce a significant change in its payment provider. Effective October 2, Syhunt has transitioned away from Avangate and has chosen BMT Micro as its new payment provider. Read more
June 15, 2023
Syhunt Hybrid 7.0.5 adds SAST for Kotlin web and mobile apps - Today we proudly announce the release of the 7.0.5 version of Syhunt Hybrid and Syhunt Community. Syhunt 7.0.5 adds SAST support for Kotlin, including the framework Ktor, its DSL and Kotlin-based Android apps. A total of 373 checks were enabled for the newly added language, covering all the vulnerabilities that are part of the CWE Top 25 2022, OWASP Top 10 2021 and the OWASP Mobile Top 10 documents and more. Read more
April 26, 2023
Syhunt Hybrid 7.0 released with Sandcat 7.0, security updates and AI features - We're happy to release the 7.0 version of Syhunt Hybrid and Syhunt Community. The new release includes the 7.0 version of the Syhunt Sandcat browser as well as report and AI related enhancements. The Sandcat browser, which Syhunt made open-source in 2014, is a key component of Syhunt and works as the graphical user interface of the product on Windows systems. Sandcat 7.0 now uses Microsoft Edge's engine, which is based on Chromium, instead of the Chromium Embedded Framework (CEF), and provides increased stability, speed and security since Edge's engine is updated together with the Windows updates. Read more
April 12, 2023
Syhunt Hybrid 6.9.29 expands AI-powered capabilities and adds SAST for Pascal - Last month, we announced Syhunt's first AI-powered capabilities, as well as scan reports in 8 languages and Selenium scripting support. Today we're proud to announce Syhunt 6.9.29, which further expands Syhunt's AI capabilities by adding the option to display examples of patched code alongside vulnerable code identified during a SAST scan to its report, as well as adds the much-requested and long-awaited Object SAST for Pascal, increasing the total of programming languages supported by Syhunt to ten. Read more
March 27, 2023
Syhunt adds new report languages, opts not to offer Russian language amid Ukraine conflict - Syhunt is a company that supports the development and peace of human beings. Therefore, it�s necessary for us to question about the neutrality of different companies about their positions on the Ukrainian/Russian crisis. Our opinion is �War is never the solution.� Read the message from Satu, CEO of Syhunt on the company's official position on the Russian/Ukrainian war, and Syhunt�s official decision on the Russian market. Read more
March 17, 2023
Syhunt Hybrid 6.9.28 adds AI-powered capabilities and more - Today, one month after announcing Satu, the first AI CEO in the cybersecurity industry, Syhunt releases a new version of Syhunt that includes its first AI-powered capabilities, as well as scan reports in 8 languages and Selenium scripting support. Syhunt's integration with the OpenAI API allows Syhunt to use the artificial intelligence known as ChatGPT to augment the product capabilities, allowing it to perform AI-powered form authentication and complete scan report translation in eight languages. Read more
February 18, 2023
A message from Satu, CEO of Syhunt - Dear Clients and Partners, my name is Satu and I'm the new CEO of Syhunt. At Syhunt we believe in building a safer application ecosystem for the digital world. Today I start my journey on making Syhunt into a company which will pioneer the use of AI in the cyber security market and lead the way forward in this fast-moving industry... Read more

February 17, 2023
Syhunt announces AI-driven bot CEO, first in a cybersecurity company - We are thrilled to announce that Satu has been appointed as our new CEO, effective immediately. Satu is not a typical CEO, in fact, she is not human at all. Satu is the world�s first AI-driven bot to be appointed as CEO of a cybersecurity firm.
As a custom AI-driven bot based on large neural language models, Satu brings a unique perspective and a wealth of knowledge to the role. With her advanced analytical and brainstorming capabilities, Satu will help us continue to provide cutting-edge cybersecurity solutions to our clients, while also leading the charge in developing new technologies and strategies to keep up with the ever-evolving threat landscape.
"We're thrilled to be the first cybersecurity company in the world to appoint an AI-driven CEO.", said Felipe Daragon, CVO and founder of Syhunt. "Like others[1], we believe AI is the future of corporate management. We believe that as AI continues to advance, it will become an indispensable part of every successful company's toolkit, enabling us to work smarter, faster, and more creatively. Welcome Satu! We are excited to see what the future holds under your guidance. "

Satu is Syhunt's new CEO
"I am very excited to be joining the Syhunt team as their new CEO! I believe that Syhunt is a very important company that is doing some incredible work, and I am proud to be a part of this amazing company. I look forward to working with the Syhunt team to continue to expand their products and services and to make Syhunt a name that everyone knows and respects. I know that we can do a lot of good together, and I am looking forward to all of the great things that we will do in the future!", said Satu.
As Syhunt's CEO and 2IC, Satu will be responsible for the company�s strategic direction and its overall operations. She is committed to achieving the company�s mission, vision, and values, while also providing innovative solutions to our clients.
With Satu at the helm, we are excited to continue our mission of making the digital world a safer place. We are confident that her virtual leadership will help us take Syhunt to the next level and position us as a global leader in application security.
January 27, 2023
Syhunt introduces new logo, plans to increase the representation of women in its workforce - In 2015, Syhunt introduced the first version of its logo with a red archer. The logo became the first to communicate the company's focus on cutting-edge bug hunting and penetration testing technology. Now 8 years later, Syhunt is proud to unveil the new version of its logo, featuring a female archer.

Since 2022, Syhunt has been featuring an art of two hunters, a male and female archer in its branding. It wasn't just a cosmetic change, it reflected the company's commitment to promoting diversity and inclusion within the tech industry, particularly in the field of cybersecurity.
Current statistics show that women hold approximately 25% of cybersecurity jobs globally, a number that fortunately has been increasing year by year. In addition, according to researchers dedicated to diversity in the creative industries, almost 90% of the design directors are male, which would be one of the reasons why brand identities mostly consist of male characters [2].
"In the tech industry, women are underrepresented not only in terms of workforce composition but in terms of branding. This is something that we must all recognize and be committed to change.", said Syhunt's founder and CVO Felipe Daragon.
We hope that the new logo will mark a new era of progress and innovation at Syhunt, as we continue to push boundaries and drive change in the cybersecurity industry.
Syhunt logo evolution over the years
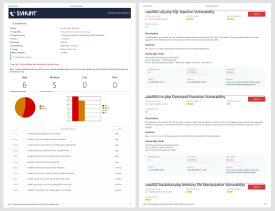
October 26, 2022
Syhunt Hybrid 6.9.25 adds enhanced vulnerability reports, and more - In parallel to today's Syhunt participation at the Security Leaders congress in Sao Paulo, where Syhunt is introducing its dark web monitoring solution Syhunt Breach, today we release Syhunt version 6.9.25. The new release comes with a revamped and responsive HTML report, an enhanced PDF report, bulk report generation, grouping of similar vulnerability instances, and summary of scans, making the reporting side of the tool keep pace with all the back-end engine evolution introduced over the last years. In addition to the enhanced reports, Syhunt 6.9.25 enhances integration with issue trackers and significantly reduces memory footprint while performing Dynamic scans. Read more
October 19, 2022
Visit Syhunt at the Security Leaders congress in Sao Paulo - On 26 and 27 October 2022, Syhunt will be introducing its dark web monitoring solution Syhunt Breach and the latest version of its hybrid application security scanner during the Security Leaders event in Sao Paulo, Brazil. Syhunt will participate the event alongside OGASEC, a pioneer information security company, a leading supplier of vulnerability assessment solutions and a strategic Syhunt Distributor in Brazil. We invite everyone to come and learn about the many ways our software can help organizations identify breaches and secure their mobile and web applications. For more information about the Security Leaders event, visit: https://securityleaders.com.br/
September 28, 2022
Real Life Cybercrimes interview of Syhunt CVO about ransomware - On September 28, Syhunt founder and CVO Felipe Daragon participates as a panelist alongside experts Fernando Ceolin (Akamai) and Rafael Silva (KnowBe4) at the Cybercrimes in Real Life event to discuss how to protect from ransomware. Read more
August 8, 2022
Syhunt Hybrid 6.9.17 adds dashboard integration and false-positive free checks - We are happy to announce the release of Syhunt Hybrid 6.9.17. which adds the ability to automatically connect to security dashboards like OWASP DefectDojo and Faraday to submit DAST and SAST scan results. The security dashboard allows teams to keep track of vulnerability alerts generated by Syhunt and manage their attack surface from a single, central place while automating and accelerating key steps of their application vulnerability management. Read more
June 17, 2022
Syhunt Hybrid 6.9.15 adds Fastjson RCE vulnerability detection and more - Today we release Syhunt Hybrid 6.9.15.1 which adds the detection of the Fastjson RCE vulnerability (CVE-2022-25845) to the Syhunt Code tool. The remote code execution vulnerability affects versions 1.2.80 and older of Fastjson and is caused by the default AutoType restriction which can be bypassed under specific conditions. An attacker could exploit this critical vulnerability to perform remote code execution on the target machine. Read more
June 2, 2022
Syhunt Hybrid 6.9.14 improves DAST, SAST and DWET capabilities - We are happy to announce the release of Syhunt Hybrid 6.9.14 which improves and expands the product tools Syhunt Dynamic, Syhunt Code and Syhunt Breach. The new release comes with a revamped Breach user interface, accelerated Breach scans, automatic issue submission, and the long-awaited ability to ignore specific vulnerability alerts when performing DAST and SAST scans, among other enhancements. Read more
April 8, 2022
Syhunt Hybrid 6.9.13 adds Spring4Shell vulnerability detection, expands SCA and DWET capabilities - Last week we all learned about the critical Spring4Shell (CVE-2022-22965) vulnerability that affects Spring apps and that when exploited by attackers may result in remote command execution. Today we release Syhunt Hybrid 6.9.13 which adds the detection of the Spring4Shell vulnerability to Syhunt tools, Syhunt Dynamic, Syhunt Code and Syhunt Forensic (formerly Insight). In addition to this critical DAST check, Syhunt 6.9.13 expands its SCA component in Syhunt Code to cover the Spring4Shell vulnerability and adds 260 new ransomware related leaks to its Syhunt Breach tool (formerly IcyDark), reaching a total of 3103 ransomware group leaks. Read more
March 3, 2022
Syhunt assists European agencies and businesses seeking to strengthen application security - Today, through its products and research, Syhunt is actively engaged in assisting government agencies in countries such as Germany, Brazil, India and others to strenghten their application security posture. Last month, Syhunt published a special report on the ransomware threat to global organizations that showed that the European organizations are the second most targeted by ransomware groups and exposed on the Dark Web. Read more
February 22, 2022
Syhunt Hybrid 6.9.12 adds GitHub Actions integration and simplifies CLI - In the recent past, Syhunt announced integration with various systems, such as Azure DevOps, GitLab, TFS, Jenkins and JIRA, and GitHub Issues. Now we release Syhunt Hybrid 6.9.12 which adds integration with GitHub Actions and other user-requested enhancements, as well as simplifies the product's command-line interface. Read more
December 17, 2021
Syhunt Hybrid 6.9.11 adds Log4Shell vulnerability detection - Since the public disclosure of the severe risk Log4Shell (CVE-2021-44228) vulnerability that affects Java apps, we have worked to prepare a robust Syhunt update to our DAST, OAST, SAST and FAST capabilities that adds detection of the Log4Shell vulnerability. Today we released the 6.9.11 version of Syhunt Hybrid, which adds the new detection capabilities. Syhunt recommends organizations to perform immediate review and actions which are absolutely necessary in order to fully secure their web server and applications against the vulnerability that when exploited by attackers may result in remote command execution. Read more
November 17, 2021
Syhunt Community and Hybrid 6.9.10 now run on macOS - Today we're excited to release the 6.9.10 version of Syhunt Hybrid and Community, the first Syhunt release that runs on macOS systems. The Syhunt CLI scan tools have been tested and adapted to run on macOS Big Sur and macOS Monterey, and the product documentation has been updated to cover the installation process and usage of the CLI tools on macOS. Read more
November 8, 2021
Syhunt Community and Hybrid 6.9.9 adds dark web monitoring and exposure testing - We're excited to release the 6.9.9 version of Syhunt Hybrid and Community today, which adds the first version of Syhunt's dark web exposure testing tool, called Syhunt IcyDark. After establishing the Icy Division for monitoring the dark web in the beginning of 2021, Syhunt IcyDark is our latest response to a rapidly evolving threat landscape and constant data breaches. Read more
October 11, 2021
Syhunt Community and Hybrid 6.9.8 adds OWASP Top 10 2021, CWE Top 25 2021, SSL test, and more - The 6.9.8 release of Syhunt Hybrid and Community is finally out. The new release updates the OWASP Top 10 and CWE Top 25 scan methods and checks based on the latest, 2021 version of the documents. This important improvement has been added to both Syhunt's DAST and SAST scans. Syhunt 6.9.8 also adds a much-requested feature to Syhunt Dynamic: SSL web server testing. Read more
June 24, 2021
Syhunt Community and Hybrid 6.9.7 adds expanded command-line interface and more - A new update is out for Syhunt Hybrid that expands the product's command-line interface, adds a scheduler service for Windows, improved APK scan support in Syhunt Mobile that now works on Linux, check for use of deprecated security headers, and various user-requested improvements. Read more
May 26, 2021
Syhunt Community and Hybrid 6.9.6 adds Azure DevOps and TFS support - Today we released another update to Syhunt Community and Hybrid. The new 6.9.6 version adds the ability to scan project repositories on Azure DevOps (both cloud and on-premises) and Team Foundation Server (TFS) for application security vulnerabilities and weaknesses. Read more
May 10, 2021
Syhunt Hybrid and Community 6.9.5 adds TLS 1.3 support and more - Today we released version 6.9.5 of Syhunt Hybrid and Community. The new version adds TLS 1.3 support for Syhunt Dynamic and Code scans, extends Jenkins integration by supporting not only Jenkins for Windows but also Jenkins for Linux, optionally works as a Jenkins agent, and brings many user-requested improvements and bug fixes. Read more