What's New in Syhunt 7.0.11
January 23, 2024
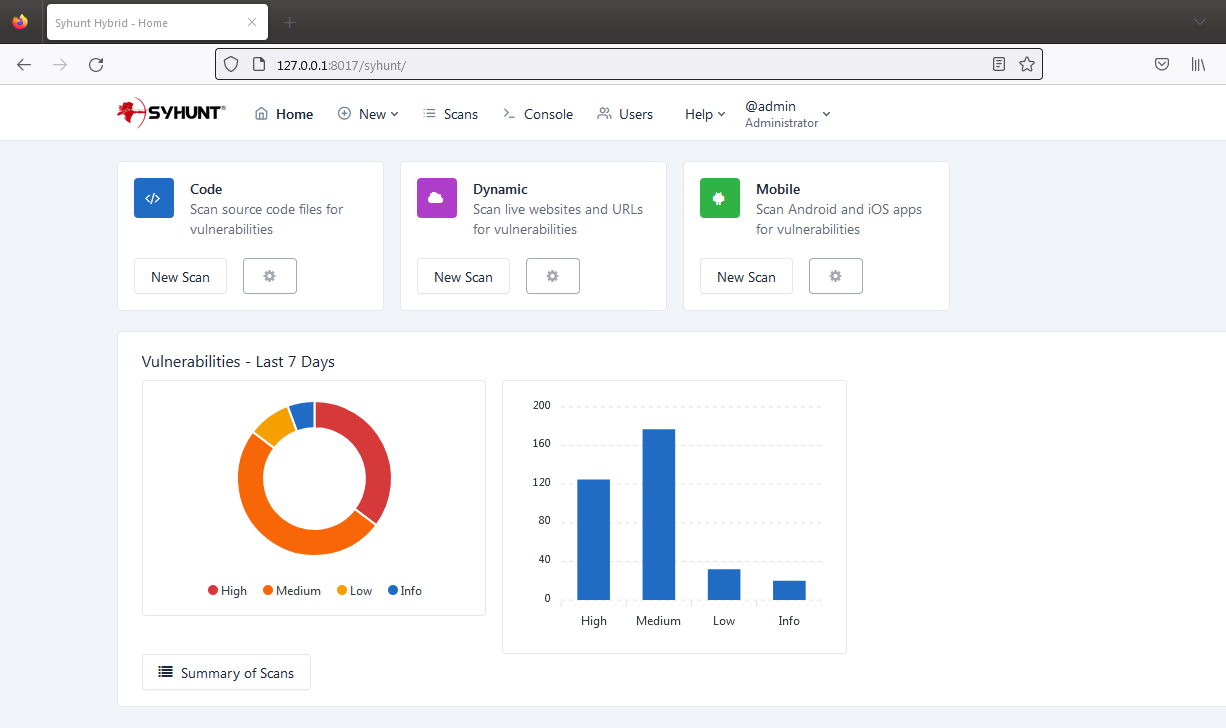
Syhunt Hybrid 7.0.11 adds web interface and 8 languages
We are excited to announce the launch of Syhunt Hybrid version 7.0.11, a significant update that introduces the highly anticipated web interface for Syhunt. This interface enables users to initiate DAST, SAST, and MAST scans, review scan results (including those initiated via the GUI, CLI, REST API, and scheduler, if used), generate detailed reports and exports, manage user accounts and permissions, oversee active sessions, execute console commands, and much more. Additionally, the interface supports eight languages: English, German, Spanish, French, Italian, Japanese, Korean, and Portuguese, with the option to produce reports in any of these languages.
The web interface of Syhunt Hybrid is built on the robust Openresty web server (a blend of Nginx and Lua) and incorporates advanced security measures such as Bcrypt for password hashing with a high complexity factor, secure session ID creation, and brute force attack protection for login processes. This new update is a game-changer, bringing a versatile web interface that operates identically on both Windows and Linux platforms.
Changes to Syhunt Breach and Discontinuation of Breach license
In October 2022, Syhunt redefined its approach to data breach detection and prevention by revamping Syhunt Breach into an integrated suite of tools. This suite includes Syhunt Forensic and DWET (Dark Web Exposure Testing). Leveraging the expertise of its AI division, Syhunt is currently reimagining the Breach suite. This transformation emphasizes the introduction of innovative tools and capabilities throughout 2024, and notably, the integration of its advanced scoring capabilities with findings from Syhunt Dynamic.
As part of this continuous evolution, Syhunt has transitioned away from offering Breach as an independent product. Instead, Breach will now be incorporated as an enhanced feature within the Dynamic Plus or Hybrid licenses. This strategic move aligns with the company's renewed focus on augmenting its third-party risk scoring abilities. In this new phase, the tool will shift away from providing direct access to breach contents, such as viewing leaked passwords or files, to mapping third-party risk and introducing new AI-powered capabilities.
Additional Improvements in 7.0.11
- Added a compliance template for the 2023 CWE Top 25 Most Dangerous Software Errors.
- Added Kotlin to technologies tab in Site Preferences.
- Added an option to specify WAF presence to technologies tab of Site Preferences.
- Added an option that allows to define a criticality level for a Dynamic target in the Site Preferences screen. The criticality level and WAF status of a target is now displayed in a new column within the Scheduler.
- Added: documented integration with Faraday. Faraday is an alternative to OWASP DefectDojo.
- Improved interprocess commmunication.
- Improved manual scan in Sandcat Browser (improved session handling)
- Improved: URLs in Exclusions in site preferences now match variants of the same URL with parameters.
- Improved detection of GIT URL in Syhunt Code.
- Automatically compacts scan cache and logs at the end of each scan to save disk space.
- Fixed: a permission issue when Scheduler is used that affected the retrieval of status of scans launched by non-admin processes (Status Canceled when the scan was still running).
- Fixed: REST API server launching when performed from account without admin privileges.
- Fixed: library conflict when running REST API server after upgrading to new openresty server.
- Fixed: bad request error when trying to submit results to GitLab tracker using -tk parameter.
- Fixed: Ignore ID setting in site preferences not working for URLs that have a path.
That's all, for now. Happy bug hunting!
