Integrating Syhunt with DefectDojo
The information in this document applies to version 6.9.17 of Syhunt Hybrid.
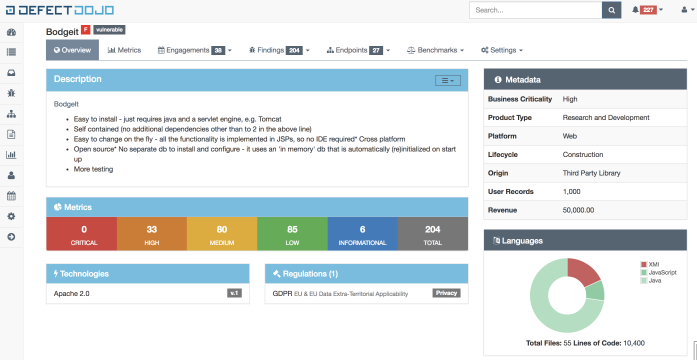
DefectDojo is a security tool that automates application security vulnerability management. DefectDojo streamlines the application security testing process by offering features such as importing third party security findings, merging and de-duping, integration with Jira, templating, report generation and security metrics.
Since version 6.9.17, Syhunt can be configured to automatically connect to the API of a DefectDojo server and submit a SAST or DAST report. Alternatively, Syhunt can generate a compatible report that can be manually imported into DefectDojo.
Auto Submiting Results
Configuring the integration with DefectDojo is an easy task and after that vulnerabilities can be automatically submitted to its dashboard.
Firstly, you have to add a DefectDojo tracker:
- Click the Issue Trackers icon
 in the launcher toolbar. The Issue Trackers screen will open.
in the launcher toolbar. The Issue Trackers screen will open.
- Click the Add Tracker icon
 in the Issue Trackers screen toolbar and choose the Add tracker: DefectDojo menu option.
in the Issue Trackers screen toolbar and choose the Add tracker: DefectDojo menu option.
- Enter a reference name for the new tracker (like MyDefectDojo) and hit OK. A preferences dialog window will open.
- Enter the DefectDojo Server URL, eg:
https://[IP]/ - Enter your token and click the OK button.
The tracker is ready! Right click the item you just edited in the list and click the Submit Test option. If you configured everything properly, a test scan item should be created at https://[server]//engagement/active. If not, you will see an error message giving a hint of what needs to be done.
Finally, associate the DefectDojo tracker to a scan:
- Through the CLI, pass the parameter -tk:[trackername]
- Through the Scheduled Scan preferences dialog, go to the Notifications tab and select the newly created tracker within Tracker Notifications.
Creating the Tracker through the CLI
If you are using the CLI version of Syhunt, you can add the tracker using the commands indicated below.
-- Example 1 - Adding a new DefectDojo tracker
scancore -tracker:add
-- Specify the type DefectDojo and the name of the tracker, and press enter
-- Configure the tracker
scancore -tracker:set to:mytrackername -key:api.url -v:"https://serverurl/"
scancore -tracker:set to:mytrackername -key:auth.token.encrypted -vsecret
-- Testing the tracker
scancore -tracker:send -tid:TEST -to:mytrackername
-- Optional settings
scancore -tracker:set to:mytrackername -key:scan.minseverity -v:Info
scancore -tracker:set to:mytrackername -key:scan.testtitle -v:"Syhunt Scan"
scancore -tracker:set to:mytrackername -key:scan.engagementname -v:"Syhunt Hybrid Scan"
scancore -tracker:set to:mytrackername -key:scan.producttypename -v:"Research and Development"
scancore -tracker:set to:mytrackername -key:scan.productname -v:Syhunt
scancore -tracker:set to:mytrackername -key:scan.autocreatecontext -v:true
scancore -tracker:set to:mytrackername -key:scan.active -v:true
scancore -tracker:set to:mytrackername -key:scan.verified -v:true
scancore -tracker:set to:mytrackername -key:scan.closeoldfindings -v:false
scancore -tracker:set to:mytrackername -key:scan.pushtojira -v:false
Generating Compatible Report
If you prefer to manually import results, Syhunt is able to generate a DefectDojo-compatible vulnerability report file. Just make sure that the output parameter is set to a filename that ends with the double extension .sast.json or .dast.json, as shown in the examples below. Finally when importing the JSON files into DefectDojo, specify the GitLab SAST or DAST format.
Note: currently, only GitLab SAST support is documented in DefectDojo. The DAST support may or may not come with some limitations
Examples
- SAST: scancode [target] -xout:anyfilename.sast.json
- DAST: scanurl [target] -xout:anyfilename.dast.json
When launching the scan through GitHub, GitLab and Powershell: use the outputex parameter of the scan function to pass the filename.
When launching the scan through Jenkins: use the outFilename parameter of the scan function to pass the filename.
For additional product documentation, visit syhunt.com/docs
