What's New in Syhunt 6.8
January 27, 2020


Syhunt expands vulnerability checks for iOS apps and missing protections in web apps
In September last year we announced support for mobile applications (Android & iOS). Now we are proud to introduce version 6.8 of Syhunt, which greatly extends its iOS check base, as well as expands its vulnerability checks for dynamic web apps. As part of this major update, we've increased the number of source code checks for Swift & Objective-C, the primary languages used for iOS app development, from 64 to 248 checks - see the full list of vulnerability checks here and a brief list of the covered categories below.
We've also added many customer-requested improvements and fixes, including new outdated Angular checks and dozens of checks for missing protections which tell when the webserver configuration can be hardened.
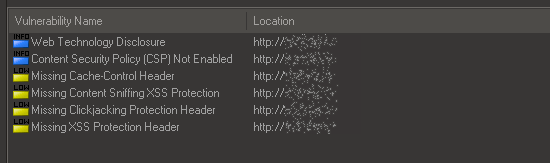
Checks for Missing Protections in Web Apps
Syhunt 6.8 adds dozens of checks for missing protection measures against attacks like clickjacking, content-sniffing XSS and others. This includes checks for missing or weak HTTP security headers, permissive HTTP Strict Transport Security (HSTS) policy, the use of deprecated policies and more.
New Mobile Checks for Swift & Objective-C
Syhunt 6.8 adds 184 new security code checks targeting the primary iOS development languages, covering:
- API Abuse & Misuse (new, to cover Biometric Authentication, SMS Usage, etc.)
- Arbitrary File Manipulation (new)
- Broken Authentication (expanded)
- Broken Cryptography (expanded)
- Cross-Site Scripting (XSS) (new)
- Code Injection (new)
- Hardcoded Sensitive Information (expanded)
- Information Leak (new)
- Insecure Communication (new)
- Insecure Data Storage (expanded to cover missing or insufficient data protection cases)
- JSON Injection (expanded)
- XML Injection (new)
- XPath Injection (new)
- Log Forging (new)
- Regular Expression Injection (new)
- Security Misconfiguration (expanded)
- Uncontrolled Format String (expanded)
- Entry Points (expanded)
The mobile support is available in limited preview in Syhunt Community and fully available to new and existing customers through a separately licensed product extension known as Syhunt Mobile.
Additional Dynamic Improvements
Additional improvements made to Syhunt Dynamic include:
- Added new crawling optimizations for heavily dynamically generated web sites.
- Improved auto form filling of dynamically adjusted fields.
- Expanded the brute force against the structure of the Start URL path.
- Fixed: a Start URL redirect handling bug involving relative paths and improved an additional case of JS redirect handling.
- Fixed: CVE reference not appearing for specific check groups.
- Fixed: Compliance report template options for web apps not appearing when using non-Platinum Plus license.
Additional Code Checks & Improvements
- Added additional XSS cases to Android checks.
- Added new outdated Angular vulnerability checks (Prototype Pollution, DoS and multiple XSS vulnerabilities).
- Added syntax highlighting of C/C++ files and analysis of C/C++ header files.
- Fixed: false positive involving version number and hardcoded resource check.
Other Improvements
- Added the ability to import targets and bookmarks from CSV and list files.
- Changed the date/time format in the Past Sessions screen and report for better visualization.
- Fixed: the user interface not highlighting when Git for Windows needs to be installed or about other fatal errors.
- Fixed: Canceled scans sometimes being listed with Scanning as status in the Past Sessions screen.
We hope you enjoy the new release!
