2014
2024 | 2023 | 2022 | 2021 | 2020 | Archive
May 22, 2014
Syhunt releases Sandcat Browser 5.0 — We're excited to announce a brand new version of our pen-test oriented web browser Sandcat (codenamed Catarinka browser). The new release will also be available as part of the 5.1 release of the Syhunt Hybrid suite. The new enhancements include: faster startup and responsiveness, huge refactoring and cleanup of the current code, latest Chromium component and improved compatibility with 64-bit Windows editions.
February 20, 2014
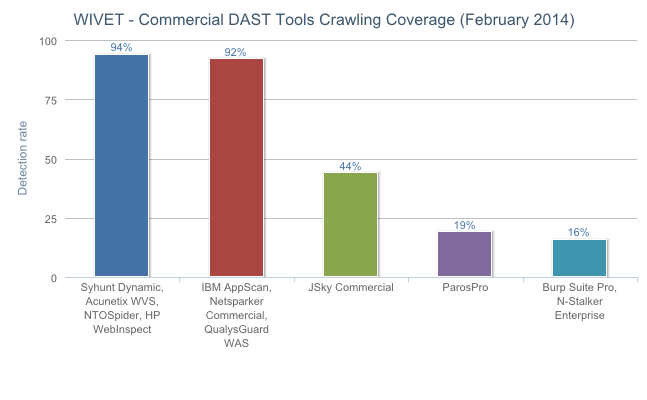
Syhunt Dynamic soars to number 1, reaches 94% crawling coverage — New WAVSEP benchmark - The WAVSEP - The Web Application Vulnerability Scanner Evaluation Project performed a massive array of tests on 63 black box web application vulnerability scanners and SAAS services. The comparison findings were published on February 5, 2014. The entire industry and security community benefits from an up-to-date comparison of today's web application security scanners like this one.
A while back — in December, we announced the release of Syhunt Dynamic 5.0 with greatly superior crawling/spidering. This year's WAVSEP data reflects the improvements that have been made in Syhunt Dynamic and shows Syhunt has the number 1 crawling coverage alongside 3 other top solutions which were able to achieve 94 percent coverage on its WIVET test.
WIVET is an open source benchmarking project that aims to statistically analyze web link extractors and adopted as an extension to the WAVSEP project. The WIVET test evaluates the scanner support for various web technologies and its ability to handle obstacles while crawling and mapping the structure of websites. According to the WAVSEP, developers, penetration testers and QA engineers need a tool with a high score in this category, especially if they prefer as much automation as possible in the web application security assessment process.
When it comes to vulnerability detection rates, Syhunt Dynamic repeated last year's performance with 100 percent detection of SQL Injection, both blind and time-based, and XSS (Cross-Site Scripting) vulnerabilities. WAVSEP used a large collection of over 1000 vulnerable test cases for 6 different attack vectors to compare the tools, which were made public simultaneously with the results.
See the full details about the WAVSEP 2014 comparison here.
February 20, 2014
Syhunt Hybrid now detects open redirect vulnerabilities - Today we are announcing that Syhunt Hybrid 5.01 is now available for download in the customer area for subscribed customers. This update expands Syhunt's extensive list of checks by bringing in the ability to locate open/unvalidated redirect vulnerabilities in web applications, an ability that is now supported by our dynamic application security testing solution, Syhunt Dynamic, our static application security testing solution, Syhunt Code, and the even more advanced Syhunt Hybrid, which combines both solutions.
Unvalidated redirects are often exploited to perform phishing attacks and used, for example, to trick users into revealing their passwords and downloading malware. The weakness, also referred to as CWE-601 by the MITRE's Common Weakness Enumeration project, is considered an OWASP violation and listed as part of their Top Ten 2013 document.
With this new addition, Syhunt now checks for over 30 classes of web application security vulnerabilities, including XSS (Cross-Site Scripting), SQL Injection, File Inclusion and Command Execution vulnerabilities. Syhunt plans to keep adding new checks and improving existing ones in future updates.
January 12, 2014
Major higher-education institution in France selects Syhunt - École Polytechnique, a higher-education and research institution in France, has selected Syhunt Hybrid for securing all its web sites and web applications. Syhunt is pleased to provide its hybrid web application security scanning solution to this customer and to other organizations in Europe and the rest of the world that are part or will be joining our customer community. Syhunt's unique scanning capabilities are allowing customers to perform deep remote assessments and code reviews of web applications like they never did before and to fix a high number of vulnerabilities they never thought existed.