Updates Archive
What's New in Syhunt 6.9.10 (November 17, 2021)



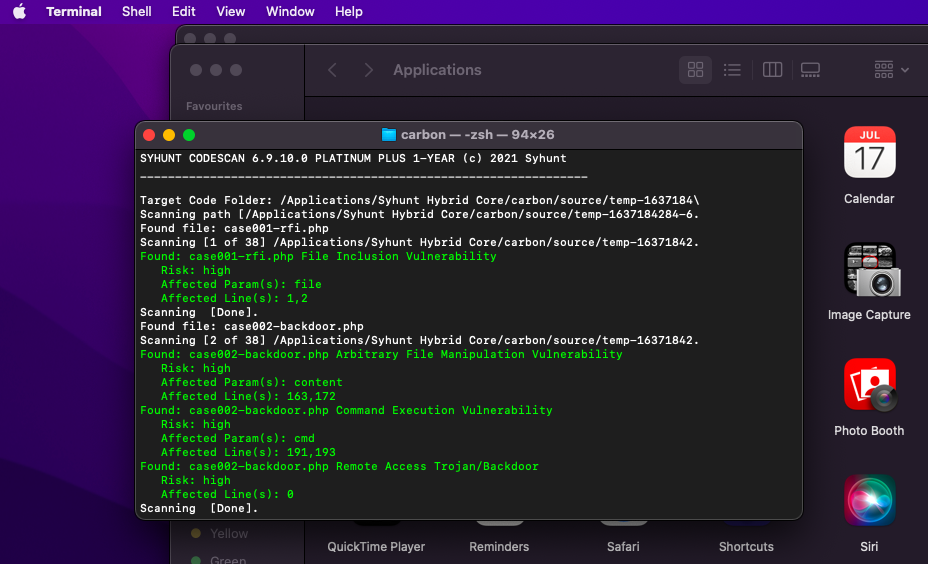
Syhunt Community and Hybrid 6.9.10 now run on macOS
Today we're excited to release the 6.9.10 version of Syhunt Hybrid and Community, the first Syhunt release that runs on macOS systems. The Syhunt CLI scan tools have been tested and adapted to run on macOS Big Sur and macOS Monterey, and the product documentation has been updated to cover the installation process and usage of the CLI tools on macOS.
To make Syhunt for macOS and every Linux distribution possible for its customers and the community, since last year Syhunt added a cross-platform, Java-based installer and worked to make its software compatible with Wine64 and expand its command-line interfaces and integration features.
Read more about Syhunt for macOS
Improvements and Changes
- Added CLI support for MacOS Big Sur and Monterey.
- Improved activation through GUI and CLI.
We hope you enjoy the new release!
What's New in Syhunt 6.9.9: IcyDark (November 8, 2021)
Syhunt Community and Hybrid 6.9.9 adds dark web monitoring and exposure testing
We're excited to release the 6.9.9 version of Syhunt Hybrid and Community today, which adds the first version of Syhunt's dark web exposure testing tool, called Syhunt IcyDark. After establishing the Icy Division for monitoring the dark web in the beginning of 2021, Syhunt IcyDark is our latest response to a rapidly evolving threat landscape and constant data breaches. Designed to help companies, organizations, government agencies and military units not only understand, but map and respond to data leaks that affect them in a more effective way, Syhunt IcyDark currently covers leaks related to over 58 million Internet domains from all over the globe.
In addition to identifying leak details through its Dark Web Exposure Testing (DWET), the full-featured Syhunt IcyDark solution allows organizations to get the privacy and security score of their Internet domains based on their track record, a unique feature called IcyScore. Syhunt IcyDark is also a dark web monitoring solution that can optionally run entirely on-premise through an unique offline mode, allowing the tool to be adopted by government agencies and military units that face restrictions in adopting cloud-based solutions.
AI-Powered
The Syhunt IcyDark software and infrastructure uses metadatabases generated by the in-house developed data leak processing bot Presta and fueled by constant human-based data leak collection and intelligence. The metadatabases cover various types of leaks and breaches, including credential exposures, file exposures, past security incidents, ransomware group leaks, and more. The digital brain behind the Icy's daily (and nightly) operations, Presta is able to analyze massive quantities of data leaks collected from the surface, deep and dark web, and uses AI (artificial intelligence) to understand leaks. Learn more
Improvements and Changes
- Added the first release of Syhunt IcyDark.
- Added Syhunt update utility for Windows.
- Improved Syhunt update utility for Linux.
- The branch parameter is now empty by default in Syhunt Code, allowing git to fetch the default branch if no branch is provided.
- Improved integration with Jenkins.
- CLI: Removed the -mcd parameter in scanurl. From now on, please use the command scancore to set depth limit
We hope you enjoy the new release!
What's New in Syhunt 6.9.8 (October 11, 2021)
Syhunt Community and Hybrid 6.9.8 adds OWASP Top 10 2021, CWE Top 25 2021, SSL test, and more
The 6.9.8 release of Syhunt Hybrid and Community is finally out. The new release updates the OWASP Top 10 and CWE Top 25 scan methods and checks based on the latest, 2021 version of the documents. This important improvement has been added to both Syhunt's DAST and SAST scans. Syhunt 6.9.8 also adds a much-requested feature to Syhunt Dynamic: SSL web server testing. The SSL server test warns about the use of insecure SSL protocol versions and deprecated TLS versions.
Improvements and Changes
- Added checks for deprecated TLS protocol versions and insecure SSL versions.
- Added the OWASP Top 10 2021 compliance checks.
- Added the CWE/SANS Top 25 2021 compliance checks.
- Added new Wordpress-related spidering optimizations.
- Abort dynamic scan if start URL is static asset.
- Updated SSL code and improved TLS 1.3 support.
- Fixed: removed the need of admin permission request from UI (added temporarily after the last update).
- Fixed: update size of Dynamic preferences dialog to fix display issue in some screen resolutions.
- Fixed: reportgl parameter not accessible through REST API.
- API users: If you're using the REST API, remember to update your API key since the last one is now invalid.
We hope you enjoy the new release!
What's New in Syhunt 6.9.7 (June 24, 2021)

Syhunt Community and Hybrid 6.9.7 adds expanded command-line interface and more
A new update is out for Syhunt Hybrid that expands the product's command-line interface, adds a scheduler service for Windows, improved APK scan support in Syhunt Mobile that now works on Linux, check for use of deprecated security headers, and various user-requested improvements.
Improvements and Changes
- Added a scheduler service to Syhunt Hybrid for Windows that works even if you log off.
- Added compatibility with Doku wiki in Syhunt Dynamic.
- Allow updating preferences through command-line interface. More
- Allow redefining the risk of a vulnerability by its unique check ID. More
- Allow unique check ID (checkid) in vulnerability ignore rules.
- Improved issue tracker updating through CLI More
- Improved and documented the Syhunt Lua API More
- Improved APK analysis, added compatibility with Java 11 and enabled APK analysis support for Syhunt Mobile on Linux.
- Improved internal crawling rules.
- Updated security header checks in Syhunt Dynamic (warn about the use of deprecated headers).
- Fixed: GIT URL in Azure DevOps Server not being accepted.
- Fixed: missing fatal error for SSL_ERROR_RX_RECORD_TOO_LONG in Dynamic.
- Fixed: a few false positive cases in Hardcoded Password and Unprotected Resources categories in Syhunt Code.
We hope you enjoy the new release!
What's New in Syhunt 6.9.6 (May 26, 2021)
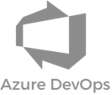

Syhunt Community and Hybrid 6.9.6 adds Azure DevOps and TFS support
Today we released another update to Syhunt Community and Hybrid. The new 6.9.6 version adds the ability to scan project repositories on Azure DevOps (both cloud and on-premises) and Team Foundation Server (TFS) for application security vulnerabilities and weaknesses. The new feature that allows to scan Azure and TFS project addresses is available through the Syhunt Code GUI and the CLI tool scancode for Windows, complements Syhunt's ability to scan GIT URLs and expands the product's list of available integrations, which today also includes PowerShell integration on Windows operating systems.
Syhunt 6.9.6's TFVC support is compatible with today's modern Azure DevOps Services and servers, and TFS 2018 down to 2010 and was made possible thanks to a free project from Microsoft MVP Neno Loje.
Read more about the integration with DevOps and TFS
Improvements and Changes
- Added the ability to code scan Azure DevOps and TFVC/TFS project URLs. More
- Added -excp CLI parameter in scancode, which allows to specify a list of paths to be excluded from the analysis.
- Added JSON report to scans launched through REST API, including GitLab compatible output format.
- Improved crawling of versioned JavaScript in Syhunt Dynamic.
- Warn when target repository URL is empty or invalid.
We hope you enjoy the new release!
What's New in Syhunt 6.9.5 (May 10, 2021)
Syhunt Hybrid and Community 6.9.5 adds TLS 1.3 support, extends Jenkins integration, and more
Today we released version 6.9.5 of Syhunt Hybrid and Community. The new version adds TLS 1.3 support for Syhunt Dynamic and Code scans, extends Jenkins integration by supporting not only Jenkins for Windows but also Jenkins for Linux, optionally works as a Jenkins agent, and brings many user-requested improvements and bug fixes.
Improvements and Changes
- Added TLS 1.3 support for Syhunt Dynamic and Code scans. As part of an upcoming release, Syhunt also plans to add TLS 1.3 support to the Syhunt Sandcat browser.
- Added integration with Jenkins for Linux and updated Jenkins extension to work with the latest Jenkins version and with Jenkins agents.
- Added detection of additional CVEs that affect JBoss and OpenSSL.
- Added last run time column to scan scheduler.
- Improved outdated software checks accuracy.
- Improved vulnerability editing dialog opening.
- Improved cookie management in Syhunt Dynamic.
- Improved enforcing of depth limit during crawling.
- Improved accuracy of time-based injection checks.
- Allow depth limit zero, which makes the spider not to crawl pages beyond the first page.
- Extended passive analysis (SQL errors).
- Fixed: internal links in table of contents not working in PDF report.
- Fixed: some temporary files not being removed from disk after scheduled code scan execution against GIT URLs.
- Fixed: control panel web backdoor false positive.
- Fixed: error when code scanning malformed UTF8 files.
We hope you enjoy the new release!
What's New in Syhunt 6.9.3 (November 3, 2020)


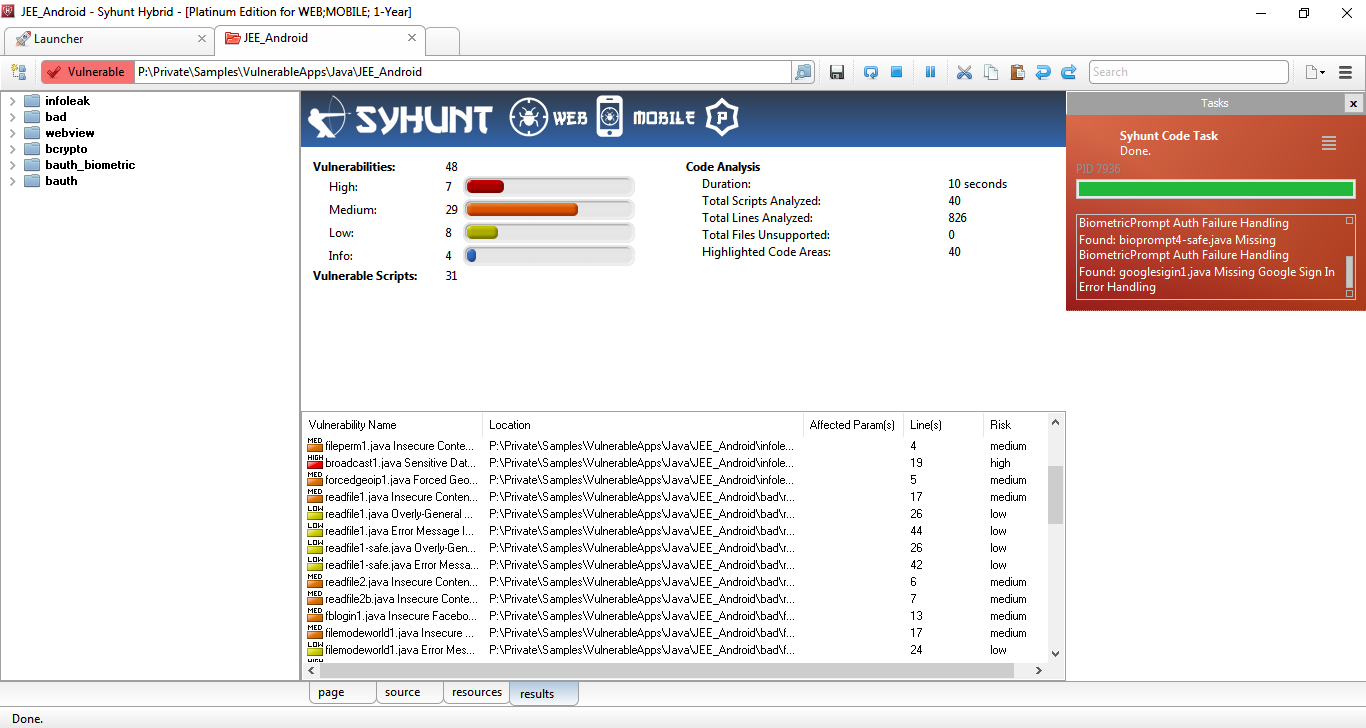
Syhunt Hybrid and Community 6.9.3 extends its TypeScript analysis, accelerates SAST and more
In August we announced 3x faster incremental scans. Now we are proud to introduce version 6.9.3 of Syhunt, which extends static analysis of TypeScript code, adds 5x faster source code scans and faster analysis of JavaScript code, includes Huntpad 2.0, as well as introduces a large number of enhancements that translate to improved DAST and SAST accuracy and performance. Version 6.9.3's focus is once again JavaScript and the MEAN stack - last year Syhunt added a large number of vulnerability checks tailored for MongoDB, Express.js, Angular (v2 and higher), AngularJS, Node.js, Koa.js and jQuery and initial code support for TypeScript. Now we took it to the next level.
Whether your TypeScript code transpiles to client-side browser or server-side JavaScript, Syhunt 6.9.3 is now equipped to perform its security analysis through its SAST capabilities and uncover vulnerabilities, weaknesses and quality issues before the code is compiled to JavaScript.
New Code Checks & Improvements
- Around 5x faster code scans, and optimizations to accelerate scans of JavaScript code.
- Greatly extended and improved TypeScript checks and analysis.
- Greatly improved SAST of Ruby, ASP (classic) and JavaScript web apps (additional accuracy and checks). Improved auto-detection of JavaScript type.
- Improved input validation analysis in a variety of languages, including ASP and JavaScript web apps.
- Added Affected Variable(s) to vulnerability properties dialog and report, and improved variable usage analysis.
- Added list of unsupported files to coverage section in report.
Huntpad 2.0 - The Bug Hunter's Notepad
Two years after the first release of Syhunt Huntpad, we're excited to release Huntpad 2.0 x64 with various new additions and improvements, including a secure random password generator and the out-of-the-box ability to execute scripts in 12 different programming languages, including various JavaScript engines and TypeScript. Why so many languages? Every code reviewer, bug hunter and penetration tester knows that it is very useful to have a way of quickly testing small pieces of code and scripts before trying on a real target environment.
Other Improvements and Changes
- Improved Syhunt Dynamic spidering - Improved JS analysis, improved JS string handling and improved form handling of forms with multiple submission methods. Improved JS parser loading under Linux.
- Faster Dynamic scans - Faster unvalidated redirect and OAST checks and faster CWE Top 25 and OWASP Top 10 scans.
- Added the Application Scan (Server-Side Focused) hunt method, which allows to scan for server-side vulnerabilities only.
- Added unique check ID for checks in Dynamic and Code check base.
- Added ISO/IEC 27001 compliance report.
- Added detection of new Node.js-based web backdoors and fixed a false positive case of JS shell.
- Improved Issue Tracker integration - Allow comma-separated emails in To field when configuring an email-based issue tracker. Fixed: scheduled scan report not being emailed under two specific circumstances.
- Improved incremental cache history loading.
- Fixed: session and report display of hunt method name of a scan started by Syhunt Code.
- Fixed: IP not being properly recognized in web log during web log scan in Syhunt Insight.
- Good bye to 32-bit era - From now on, only the 64-bit version of Syhunt will be available.
We hope you enjoy the new release!
What's New in Syhunt 6.9.1 (August 25, 2020)
Syhunt Hybrid and Community 6.9.1 Adds 3.5x Faster, Incremental Scans
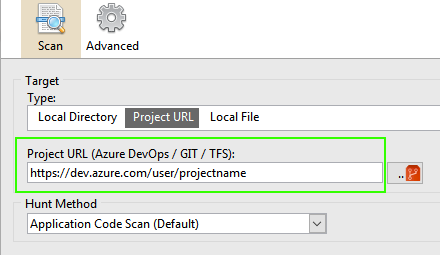
Today we announce yet another update for Syhunt Hybrid and Community, with the addition of 3.5x faster, incremental DAST and SAST analysis. With the new feature available in Syhunt 6.9.1, results and data from scans against a specific target URL or codebase are automatically stored and used to speed up future scans.
To give an idea on how important this new feature is, a dynamic scan against the PreyServer (our vulnerable demo web app) which usually has a duration of 2m10 got reduced to just 38 seconds with incremental scan after the first scan has been executed. In a very similar way, a code scan against a very large test codebase with a duration of 6m21 got reduced to 1m49 after the first scan.
All Syhunt scans are now by default incremental scans. Syhunt will automatically manage the new feature, discarding its cached incremental scan data when appropriate.
Other Improvements
- Added check for SQUID-2020 Cache Poisoning Issue in HTTP Request processing (CVE-2020-15049)
- Allow incremental scan to be enabled or disabled from site preferences and schedule preferences dialogs (enabled by default).
- Allow incremental scan data to be manually cleared from the Dynamic Targets and Scheduled Scans lists. Events such as upgrading Syhunt or 90 days passed since the incremental cache was created will make Syhunt automatically reset its incremental cache.
- Added -inc parameter that allows to set the incremental scan mode in ScanURL and ScanCode CLI tools.
- Improved scan scheduler (Improved list of scheduled scans with new columns and icons, added the Scan Scheduler to the Launcher screen, allow to rename a scheduled scan, and more).
- Allow columns to be sorted.
- Bug fixes: the status of a scan in progress being reported as Cancelled in the past sessions screen (bug introduced in 6.9.0.0), the Target column will display proper target name for new scans in the past sessions screen, and fixed a hash generation problem that would rarely cause a crash.
We hope you enjoy the new release!
What's New in Syhunt 6.9 (August 4, 2020)



and more
Syhunt Hybrid and Community 6.9 now runs on modern Linux distributions
Note (August 9): We successfully tested Syhunt 6.9 on additional Linux distros and versions: Debian 9 and 10, CentOS 8 Minimal, Manjaro 19, Linux Mint 20, MX Linux 19 and Elementary OS 5.1.
We're excited to announce the immediate release of Syhunt Hybrid and Syhunt Community version 6.9, the first Syhunt release to embrace cross-platform integration. In the recent past, Syhunt embraced open-source development, by releasing the source code of the Syhunt Sandcat browser, Huntpad, and many other core software and libraries the company developed and actively maintains. With today's release, Syhunt 6.9 just runs, out-of-the-box on Kali Linux and Parrot Security OS, and with almost zero effort runs on any 64-bit Linux distribution - we successfully tested Syhunt on 14 popular Linux distributions, including Ubuntu (Server and Desktop), CentOS, Fedora and openSUSE and, we documented it.
To make Syhunt for Linux possible for its customers and the community today and in the long term, Syhunt added a cross-platform, Java-based installer and worked to make its software compatible with Wine64, expand its command-line and REST-based interfaces and integration features, while at the same time Syhunt is working on native 64-bit binaries for key Linux distributions.
Read more about Syhunt for Linux
Other Improvements
- Added option to export vulnerabilities as ModSecurity CRS virtual patching rules when generating a report.
- Added manual login option to ScanURL CLI tool (parameter -atype:Manual).
- Added the ScanCore tool which allows various CLI-based operations such as update Pen-Tester Key, display keys information, generate web API key, manage and use issue trackers and more.
- Improved Scheduler with many new options and bug fixes.
- Allow by default complete export of preferences through menu -> Import & Export options with new .scpbak extension.
- Past Sessions now displays by default scans from last 7 days and can be changed to display different periods from toolbar.
- HTML report now include all required assets within the same file.
- Improved task management and setup application.
- Improved GitHub and GitLab tracker integration.
- Improved spider rules.
We hope you enjoy the new cross-platform release!
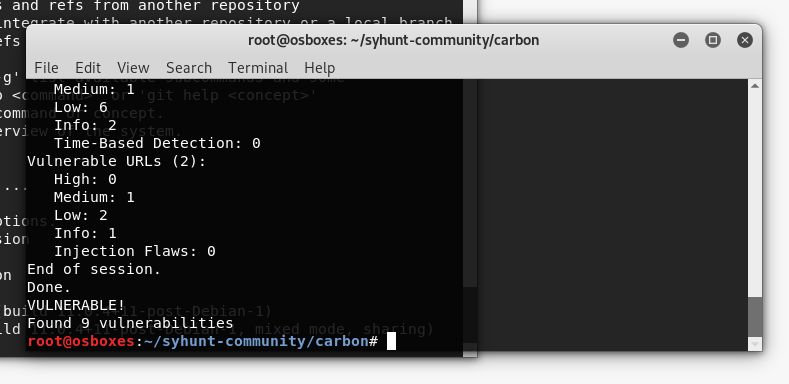
What's New in Syhunt 6.8.6 (July 1, 2020)

Syhunt Hybrid 6.8.6 now integrates with GitLab CI and PowerShell
We're proud to announce the release of Syhunt Hybrid version 6.8.6. The new version adds integration with GitLab's Continuous Integration and Security Dashboard, enabling Syhunt to continually scan web and mobile applications in repositories on GitLab.com and GitLab self-hosted versions looking for the 2019 CWE Top 25 Most Dangerous Software Errors, OWASP Top 10, OWASP Mobile Top 10 and many other vulnerabilities. The integration combines SAST and DAST methodologies within the DevOps pipeline and stages. In addition to the features above, Syhunt 6.8.6 adds integration with PowerShell, pass/fail testing and JSON export, making it quick and straightforward to integrate Syhunt to your development, testing, and deployment workflow.
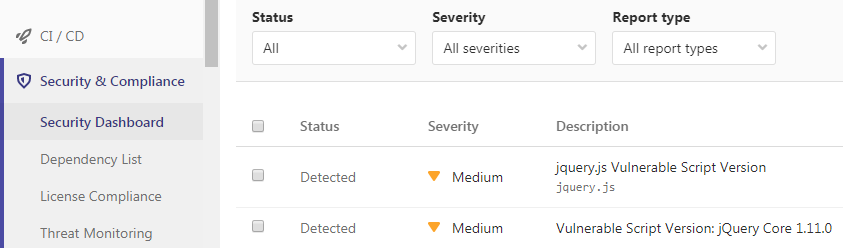
Read more about integrating Syhunt and GitLab CI/CD
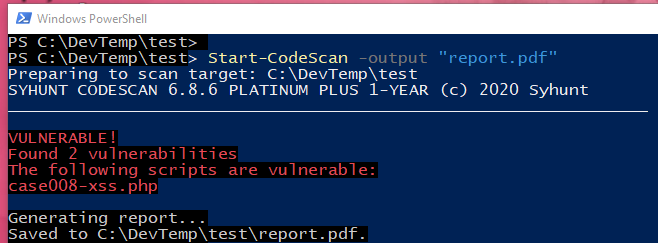
Read more about integrating Syhunt and PowerShell
Other Improvements
- Improved accuracy when checking for backup files and brute-forcing for files and directories (Syhunt Dynamic).
- Added -pfcond parameter in CLI scan tools for performing pass/fail testing.
- Added -gx and -xout parameter in CLI scan tools which allow to generate result exports in addition to reports.
- Fixed: outdated false positive involving latest mod_fcgid (Syhunt Dynamic).
- Fixed: false positive cases when analyzing ASP.Net CSharp code (Syhunt Code).
We hope you enjoy the new release!
What's New in Syhunt 6.8.5 (June 10, 2020)
Syhunt Hybrid 6.8.5 released, adds GitLab support and extends issues integration
We're happy to release Syhunt Hybrid version 6.8.5. The new release brings extended issue tracker integration with support for GitLab issues, custom labels and fields in any tracker, personal access token support, improved checks for weak or missing HTTP security headers and bug fixes.
Issue Tracker Integration Improvements
- Added GitLab issue tracker support.
- Improved Jira support: allow editing custom fields in tracker preferences screen.
- Allow editing a list of labels when configuring issue trackers of any kind.
- Allow personal access token in GitHub tracker preferences.
Improved Header Checks and Bug Fixes
The newly added checks for weak or missing security headers got its first revision which addressed two specific false positive cases:
- a Permissive HSTS Header check false positive case.
- Missing Content Sniffing XSS Protection false positive (X-Content-Type-Options).
In addition to the false positive cases above, the following bugs were addressed in Syhunt Dynamic: a TLS 1.2 handshake issue, a case of http-equiv related redirect handling issue and a bug in experimental IDS Evasion feature (disabled by default) that when the option was enabled, the request version would be set incorrectly.
We hope you enjoy the new release!
What's New in Syhunt 6.8.3 (May 1, 2020)
Note: Syhunt 6.8.4 (released in May 21) includes an update notification feature and some bug fixes.
Syhunt Hybrid 6.8.3 released, adds enhanced DAST fingerprinting, manual login and more
We're happy to release Syhunt Hybrid version 6.8.3. The new release brings many important DAST improvements, including enhanced web server fingerprinting, integration with Google Chrome and Mozilla Firefox, hybrid client-side JavaScript code analysis (SAST-within-DAST), and more.
Syhunt Hybrid 6.8.3 adds Hunter-Sense�, a fingerprinting feature that allows the detection of the hidden versions of server software and components. If an Apache or Nginx web server or server module is configured to hide its version, Syhunt Hunter-Sense is many times able to reconstruct the incomplete "picture" and determine the version number of the server and its components, such as PHP, mod_ssl, OpenSSL and Phusion Passenger. The pioneer feature is based on an analysis we conducted of patterns found in 1 million Internet websites and allows Syhunt to detect outdated, vulnerable server software and components that would go otherwise unnoticed.
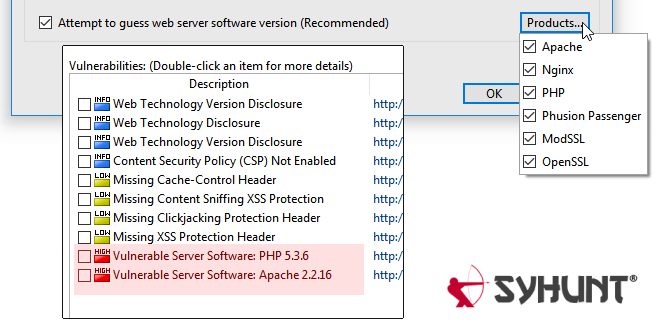
Outdated Server Sofware Detection
Syhunt Hybrid 6.8.3 adds over 1200 checks for outdated, vulnerable server software, covering over 30 web server software and components � powered by its new Hunter-Sense fingerprinting capabilities. In addition to this, Syhunt Code has been integrated with Syhunt Dynamic to perform extended hybrid analysis of client-side JavaScript - Syhunt's SAST now runs from within its DAST. This innovative SAST-within-DAST approach allows that both custom vulnerable JavaScript code and outdated, vulnerable third-party JavaScript libraries are detected client-side through dynamic analysis.
Manual Login in External Browser
Syhunt Hybrid 6.8.3 integrates with Google Chrome and Mozilla Firefox without the need of installing a browser extension. This adds the ability to launch a scan against a web application after logging in from an external web browser instance - an easy 3-step process. Alternatively, automated login and manual login through Syhunt's built-in, Chromium-based Sandcat browser is still available.

Other Improvements
- Moved crawling depth limit option and OAST option to the Site Preferences screen.
- Changed default browser emulation mode and user agent to Chrome.
- Improved parsing of JavaScript in HTML files.
- Report generation now runs in an isolated task.
- Allow SSH protocol in GIT URLs
- Fixed: crash during outdated code check when scanning known third-party script.
We hope you enjoy the new release!
What's New in Syhunt 6.8.2 (April 2, 2020)

Syhunt Hybrid 6.8.2 released, adds static code analysis of Ruby web apps and more
A new update released today brings a long-awaited feature to Syhunt: SAST for Ruby based web applications. Syhunt 6.8.2 is now able to scan the source code of web applications in Ruby (Rails and ERB) for security bugs with coverage for over 19 vulnerability categories. Of all the programming languages which have been added to Syhunt over recent years, Ruby was the only important one that was missing. In addition to this important new feature, Syhunt 6.8.2 also includes compliance reporting and scan method for the 2019 CWE Top 25 Most Dangerous Software Errors, and Imperva SecureSphere compatible vulnerability export for allowing virtual patching of new vulnerabilities as they are identified by the tool.
Code Checks for Ruby
Syhunt 6.8.2 adds source code checks for the following vulnerabilities and weaknesses in Ruby code:
- Cross-Site Scripting (XSS)
- SQL Injection
- Arbitrary File Manipulation
- Broken Cryptography
- Code Injection
- Denial of Service
- Hardcoded Sensitive Information
- HTTP Header Injection
- Insecure Communication
- Insecure Data Storage
- Information Disclosure
- Log Forging
- Bad Practices
- Weak Password Hashing
- Command Execution
- Security Misconfiguration
- Server-Side Request Forgery
- Uncontrolled Format String
- Unvalidated Redirect
Other Improvements
- Added header manipulation checks in Syhunt Dynamic.
- Added beta Imperva SecureSphere WAF XML output for virtual patching.
- Added a compliance template for the 2019 CWE Top 25 Most Dangerous Software Errors.
- Added two new scan methods: CWE Top 25 and OWASP Top 10, which allow to scan specifically for the top 25 most dangerous software errors and the 10 most critical web application security risks.
- Added an important cleanup of temporary files created during OAST testing in Syhunt Dynamic.
- Improved parsing of Python code.
We hope you enjoy the new release!
What's New in Syhunt 6.8.1 (March 6, 2020)

Syhunt introduces Hybrid-Augmented Analysis, OAST & Android APK Analysis capabilities
We are proud to introduce version 6.8.1 of Syhunt and, at the same time, unveil its online Syhunt Signal service (http://signal.syhunt.com/). The Syhunt scanner integration with Syhunt Signal adds the ability to perform OAST (Out-of-Band Application Security Testing), which allows Syhunt to detect a range of otherwise invisible, high-risk out-of-band (OOB) vulnerabilities, as well as to perform Hybrid-Augmented Analysis, a combination of DAST, SAST and OAST methodologies. Using a range of OAST techniques, Syhunt 6.8.1 is also able to demonstrate data exfiltration from a vulnerable target web server. Out-of-band (OOB) vulnerabilities are usually high-risk, such as variants of OS Command Injection, SQL Injection and XXE Injection that cannot be detected by conventional DAST, making the adoption of the OAST methodology necessary.
As part of this release, we've also expanded Syhunt's MAST (Mobile Application Security Testing) capabilites with the ability to reverse engineer and scan Android Package (APK) files for OWASP Mobile Top 10 and CWE/SANS Top 25 risks.
Hybrid-Augmented Analysis & OAST
Syhunt Hybrid simulates inferential, in-band and out-of-band (OOB) attacks by using entry point and other information acquired through SAST and a combination of DAST and OAST. Syhunt's online OAST service, known as Syhunt Signal, listens to forced requests coming in from a vulnerable target web server over the course of a scan and signals back to the Syhunt scanner. Syhunt then automatically correlates the received Signal alerts with attack requests it launched and adds the identified vulnerabilities to its report and user interface. The collaboration with Syhunt Signal also allows the Syhunt scanner to automatically exfiltrate data from a vulnerable target, which gets added to the scan results. This is achieved through different techniques (environment and OS-specific).
The OAST capability is available at no additional cost to existing Syhunt Dynamic and Syhunt Hybrid customers. The new feature needs an active Internet connection to work, so that Syhunt Dynamic can communicate with Syhunt Signal.
Out-of-Band Vulnerability Checks
Syhunt 6.8.1 adds checks for the out-of-band variants of the following vulnerabilities:
- Command Execution
- Remote File Inclusion (RFI)
- Server-Side Request Forgery (SSRF)
- SQL Injection
- XML External Entity (XXE) Injection
Android APK Analysis
Syhunt 6.81 adds the ability to scan Android Package (APK) files for vulnerabilities. The new feature is available at no additional cost to existing Syhunt Mobile, Syhunt Code Plus or Syhunt Hybrid Platinum Plus customers and allows to scan an Android application for vulnerabilities without the need of having its source code files. Despite the support for APK files, it is still recommended to scan the original mobile application source code files if available, since the APK file analysis uses reverse engineering techniques.
Other Improvements
- Added the ability to scan a single source code file from the New Scan dialog.
- Fixed: some redundant reporting of remote file inclusion vulnerabilities.
- Fixed: a problem with individual source code file scan with ScanCode CLI.
- The CLI tools now highlight in red about fatal errors.
We hope you enjoy the new release!
What's New in Syhunt 6.8 (January 27, 2020)


Syhunt expands vulnerability checks for iOS apps and missing protections in web apps
In September last year we announced support for mobile applications (Android & iOS). Now we are proud to introduce version 6.8 of Syhunt, which greatly extends its iOS check base, as well as expands its vulnerability checks for dynamic web apps. As part of this major update, we've increased the number of source code checks for Swift & Objective-C, the primary languages used for iOS app development, from 64 to 248 checks - see the full list of vulnerability checks here and a brief list of the covered categories below.
We've also added many customer-requested improvements and fixes, including new outdated Angular checks and dozens of checks for missing protections which tell when the webserver configuration can be hardened.
Checks for Missing Protections in Web Apps
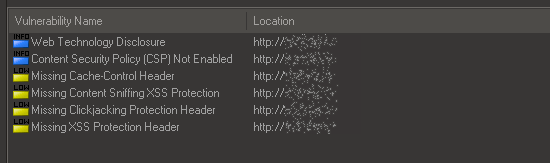
Syhunt 6.8 adds dozens of checks for missing protection measures against attacks like clickjacking, content-sniffing XSS and others. This includes checks for missing or weak HTTP security headers, permissive HTTP Strict Transport Security (HSTS) policy, the use of deprecated policies and more.
New Mobile Checks for Swift & Objective-C
Syhunt 6.8 adds 184 new security code checks targeting the primary iOS development languages, covering:
- API Abuse & Misuse (new, to cover Biometric Authentication, SMS Usage, etc.)
- Arbitrary File Manipulation (new)
- Broken Authentication (expanded)
- Broken Cryptography (expanded)
- Cross-Site Scripting (XSS) (new)
- Code Injection (new)
- Hardcoded Sensitive Information (expanded)
- Information Leak (new)
- Insecure Communication (new)
- Insecure Data Storage (expanded to cover missing or insufficient data protection cases)
- JSON Injection (expanded)
- XML Injection (new)
- XPath Injection (new)
- Log Forging (new)
- Regular Expression Injection (new)
- Security Misconfiguration (expanded)
- Uncontrolled Format String (expanded)
- Entry Points (expanded)
The mobile support is available in limited preview in Syhunt Community and fully available to new and existing customers through a separately licensed product extension known as Syhunt Mobile.
Additional Dynamic Improvements
Additional improvements made to Syhunt Dynamic include:
- Added new crawling optimizations for heavily dynamically generated web sites.
- Improved auto form filling of dynamically adjusted fields.
- Expanded the brute force against the structure of the Start URL path.
- Fixed: a Start URL redirect handling bug involving relative paths and improved an additional case of JS redirect handling.
- Fixed: CVE reference not appearing for specific check groups.
- Fixed: Compliance report template options for web apps not appearing when using non-Platinum Plus license.
Additional Code Checks & Improvements
- Added additional XSS cases to Android checks.
- Added new outdated Angular vulnerability checks (Prototype Pollution, DoS and multiple XSS vulnerabilities).
- Added syntax highlighting of C/C++ files and analysis of C/C++ header files.
- Fixed: false positive involving version number and hardcoded resource check.
Other Improvements
- Added the ability to import targets and bookmarks from CSV and list files.
- Changed the date/time format in the Past Sessions screen and report for better visualization.
- Fixed: the user interface not highlighting when Git for Windows needs to be installed or about other fatal errors.
- Fixed: Canceled scans sometimes being listed with Scanning as status in the Past Sessions screen.
We hope you enjoy the new release!
What's New in Syhunt 6.7 (September 17, 2019)



Syhunt adds support for Android and iOS apps and greatly extended checks for Java
We're excited to announce the immediate availability of Syhunt version 6.7. This release is a milestone in Syhunt's development history. It brings support for mobile (Android & iOS) applications, greatly extends its Java check base and adds the much-awaited scan scheduling feature. As part of this major update, we've added checks and support for the Swift and Objective-C programming languages, which are the primary languages used for iOS app development, and increased the number of source code checks for Java, the primary language used for Android app development, from 70 to 310 checks. The newly added features and checks, together with Syhunt's ability to scan JavaScript-based applications, including Angular and Node.js, make Syhunt suited for both mobile and web application security assessment. The new release also introduces a Mobile Compliance report template which focuses on the OWASP Mobile Top 10 risks list, as well as the CWE/SANS Top 25 Most Dangerous Software Errors and the PCI DSS v3,2.1 standard.
With this update, users of the Community edition of Syhunt will be happy to know that they can now perform a near-complete source code scan, as all code checks are now included with Syhunt Community, though the details of High-rated and specific Medium-rated vulnerabilities are only available in the professional editions of Syhunt.
The mobile support is available in limited preview in Syhunt Community and fully available to new and existing customers through a separately licensed product extension known as Syhunt Mobile. The newly added Java checks for web applications are available to existing customers at no additional cost.
New Code Checks for Java
Syhunt 6.7 adds security code checks targeting Java-based web and mobile apps, covering:
- Code Injection (CWE-94)
- Insecure Communication
- Insecure Cryptographic Algorithms (CWE-327)
- Regular Expression Injection (CWE-400)
- SQL Injection (Spring Framework)
- Uncontrolled Format String (CWE-134)
- Various bad practices
Improved and extended checks for Java include: Broken Authentication, Broken Cryptography, Security Misconfiguration, Cross-Site Scripting (XSS), Command Execution, Code Injection, File Inclusion and Manipulation, SQL Injection, LDAP Injection, XML Injection, Information Leakage, Log Forging and Denial-of-Service.
Code Checks for Swift & Objective-C
Syhunt 6.7 adds security code checks targeting the primary iOS development languages, covering:
- Broken Authentication
- Command Execution
- Insecure Communication
- Insecure Data Storage
- Insecure Hashing Algorithm
- Insecure Cryptographic Algorithms
- Uncontrolled Format String
- Hardcoded Sensitive Information
- Buffer Overflow
- Various bad practices
Other Code Improvements
- Improved vulnerability detection accuracy and vulnerable line detection precision.
- Improved insecure randomness checks (additional checks).
- Improved multi-language source code parsing.
- Additional entry point coverage and input filtering/validation analysis.
Dynamic and Other Improvements
- Improved automated web form login (alternative schemes).
- Improved spidering of heavily dynamically generated web stores.
- Minor optimizations for Wordpress-based websites.
- Added a built-in Scan Scheduler. For detailed information, see: Scheduling Scans
- Allow to ignore specific vulnerabilities in Site Preferences and Code Scanner Preferences screen.
- Improved session status and icons in session manager.
- Fixed: a few bugs and false positives (as detailed in the CHANGELOG)
We hope you enjoy the new release!
What's New in Syhunt 6.6 (June 3, 2019)

Syhunt adds SAST support for Angular, AngularJS, web services, and more
We're happy to announce that Syhunt version 6.6, released today, adds SAST support for web services, and extends support for the MEAN stack by adding support for Angular (v2 and higher) and AngularJS-based web applications, TypeScript, and a large number of additional checks covering Node.js, Express.js, jQuery, client-side JavaScript, and Java. Syhunt 6.6 also adds SAST support for Azure Repos and Electron-based apps, manual login option when performing DAST, and optimizations that speed up scans in both DAST and SAST. The extended coverage means that Syhunt is now able to scan not only the source code of web applications, but the source code of web services and JS-based desktop applications.
Code Checks for Angular & AngularJS
Syhunt 6.6 adds security code checks targeting Angular web apps, covering:
- Cross-Site Scripting (XSS) - covering JavaScript and TypeScript
- Cross-Site Request Forgery (XSRF)
- Broken Authentication
- Local Storage Usage
- Sensitive Data Stored in Local Storage
- Sensitive Information Client-Side
- Outdated Vulnerable Scripts
Code Checks for Client-Side JavaScript
- DOM-Based XSS (DOM-Based Cross-Site Scripting)
- Local Storage Usage
- Sensitive Data Stored in Local Storage
- Outdated Vulnerable Scripts, including jQuery Core, jQuery Migrate, jQuery UI, fullPage, Bootstrap and momentjs - this includes the analysis of external, online JavaScript files.
- Code Injection
- Unvalidated Redirect
- XML Injection
- Client-Side Request Forgery
- Information Disclosure (various)
- Security Misconfiguration (various)
Code Checks for Node.js
- Cross-Site Scripting (XSS)
- Denial of Service (DoS) (new)
- File Inclusion (new)
- XPath Injection (new)
- XML Injection (new)
- Server-Side Request Forgery (SSRF) (new)
- Information Disclosure (new)
- Security Misconfiguration (new)
- SQL Injection (improved)
- Code Injection (improved)
- Unvalidated Redirect (improved)
- File Manipulation (improved)
- Command Execution (improved)
- HTTP Header Injection (improved)
- Log Forging
- Input filtering/validation analysis (improved)
Additional Code Checks
Syhunt 6.6 also adds checks for:
- Broken Cryptography (new) - usage of Insecure Hashing Algorithms, Insecure Cryptographic Algorithms, Weak Protocols and Insecure Randomness.
- Insecure Salting (new) - covering all languages
- Hardcoded Sensitive Information (new), and logging of sensitive information
- Weak Password Hashing (rewritten and improved)
- Backdoor (improved)
- SQL Injection, XML Injection and Information Leak (improved for Java)
Manual Login Support
Syhun 6.6 adds the ability to start a scan against a website after manually logging in - when you start a Dynamic scan from within the Sandcat Browser the tab session data is used as part of the scan. Use of the feature is explained in the manual login section of the Syhunt Dynamic QuickStart document.
Extended GIT Support
- Added the ability to scan GIT repositories via user interface, and to create and manage a list of favorite target repositories.
- Added support for Azure Repos using GIT.
Dynamic and Other Improvements
- Improved HTTP/HTTPS protocol and SSL support (fixed: connection reset by peer error when trying to scan some websites).
- Added an option to auto follow off-domain redirect in Start URL (enabled by default in GUI and CLI)
- Ask about off-domain URL redirect when defining a dynamic target.
- Added additional Joomla-specific optimizations.
- Improved handling of popups in Sandcat Browser.
- Fixed: inability to properly pin app to the Windows taskbar.
- Fixed: many other bugs and false positives (as detailed in the CHANGELOG)
Note: Checks above in gray color are only available in the professional editions of Syhunt.
We hope you enjoy the new release!
What's New in Syhunt 6.5 (December 26, 2018)
Syhunt adds F5 BIG-IP ASM compatible vulnerability export, Jenkins extension, JIRA and GitHub integration, GIT support and more
Today we release version 6.5 of Syhunt Hybrid and Syhunt Community, a release with focus on integration with other systems such as Jenkins and F5 BIG-IP Application Security Manager (ASM), JIRA and GitHub issues, GIT source code control systems, as well as bringing UI improvements, spider improvements and framework-specific optimizations.
JIRA and GitHub Issues integration
Syhunt 6.5 is the first release to support JIRA and GitHub issues. Configuring an issue tracker is an easy task and vulnerabilities can be submitted to a specific project with the click of a button.
F5 BIG-IP ASM compatible scanner export
The F5 BIG-IP Application Security Manager (ASM) is able to import vulnerability scan results from Syhunt Dynamic scans, virtually patching vulnerable web applications - Syhunt 6.5 generates vulnerability exports compatible with the F5 BIG-IP ASM system. To generate the export, when saving a report, just select to save the file as type XML ASM.
Jenkins extensions
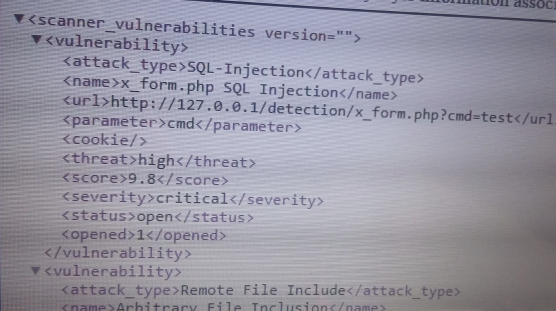
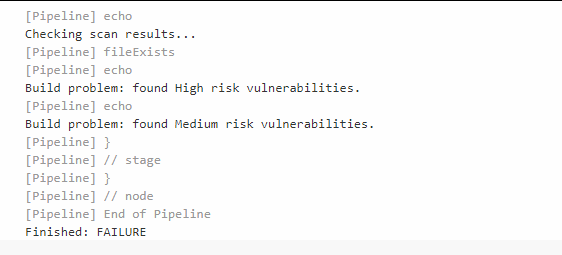
Syhunt 6.5 comes with extensions for Jenkins that allow web application security scans to be called from within a Jenkins Pipeline script, allowing customers to integrate the Syhunt Dynamic and Syhunt Code scanner tools into their continuous delivery pipeline, schedule scans and much more. The beta extensions add three Groovy functions called syhunt.scanURL(), scanCode() and scanGIT() that can be used to perform dynamic and source code scans (DAST and SAST) from within a pipeline execution, optionally failing a build if a certain criteria is met (like if High risk vulnerabilities are found).
GIT Protocol Support
Syhunt 6.5 adds support for GIT URLs in ScanCode CLI utility and Lua API, and support for GIT branches in both the CLI utility and the scanGIT() command for Jenkins. The examples below show how to scan a GIT repository.
-- from the command prompt
scancode git://sub.domain.com/repo.git
scancode https://github.com/user/repo.git -rb:master
-- from Jenkins pipeline script
syhunt.scanGIT([target: 'https://github.com/someuser/somerepo.git', branch: 'master', build: 'failifriskmedium'])
-- from Lua script
code:scanurl('https://github.com/someuser/somerepo.git', 'master')
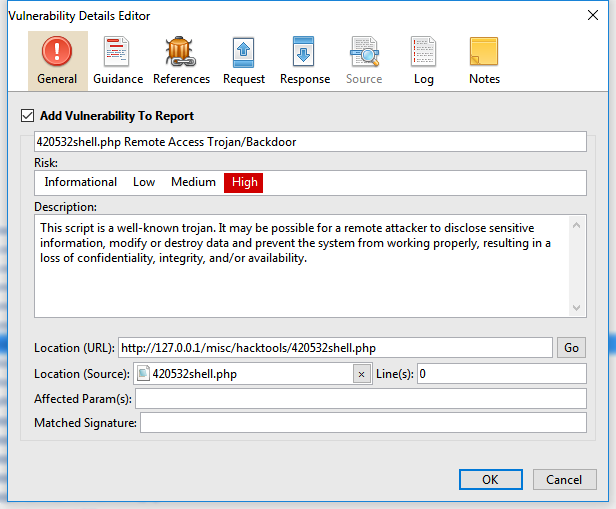
Revamped Vulnerability Details screen
Syhunt 6.5 adds a revamped vulnerability details dialog with editing capabilities.
Additional Improvements and Changes
Additional improvements in Syhunt 6.5 include:
- Added Dynamic Targets screen to launcher - allows to manage a list of common target URLs. You can access it through the purple bookmark icon
 in the Launcher toolbar or the New Scan dialog.
in the Launcher toolbar or the New Scan dialog.
- Added Rails framework, WII framework and WordPress related optimizations.
- Added the ability to import and export a scan session from/to a file.
- Reviewed hunt methods Malware Content and Structure Brute Force and enabled additional checks. Improved extension checking and structure brute force checks and fixed a false positive case.
- Faster Authentication Bypass checks.
- Improved fingerprinting and added detected languages and OS type to reports.
- Improved XML exports.
- Improved spider (improved web site caching and mapping).
- This release comes with the latest Syhunt Sandcat browser updates and drops support for Windows Vista.
We hope you enjoy the new release!
What's New in Syhunt 6.4 (October 17, 2018)
Syhunt adds PCI DSS 3.2.1 support and more
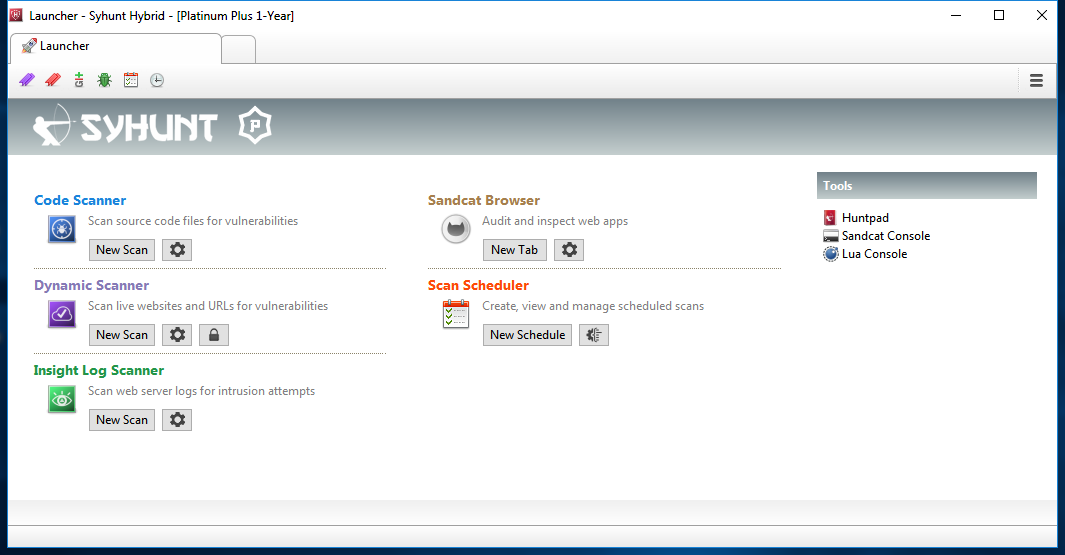
Today we release version 6.4 of Syhunt Hybrid and Syhunt Community, a release with focus on compliance report generation and user interface (GUI) enhancements. This version comes with a revamped launcher screen (see the screenshot below), adds new PCI DSS related checks (such as checking for unencrypted credit card transaction) and many new compliance report options, such as:
- PCI DSS compliance versions 3.2 and 3.2.1
- All recent OWASP lists, including the latest OWASP Top 10 list
- CWE/SANS Top 25 Most Dangerous Software Errors
- WASC (The Web Application Security Consortium) Threat Classification
Additional improvements include:
- Added 183 additional admin paths.
- Added additional password file disclosure checks.
- Added Jooma-specific optimizations.
- Added Nginx support in Syhunt Insight.
- Improved spidering (additional link extraction and improved relative path handling).
- Combined link list with additional details into new Coverage report section.
Screenshot: Revamped Launcher
We hope you enjoy the new release!
What's New in Syhunt 6.3 (September 8, 2018)

Syhunt now supports CVSS v3 vulnerability scoring
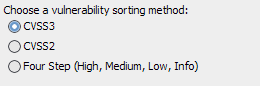
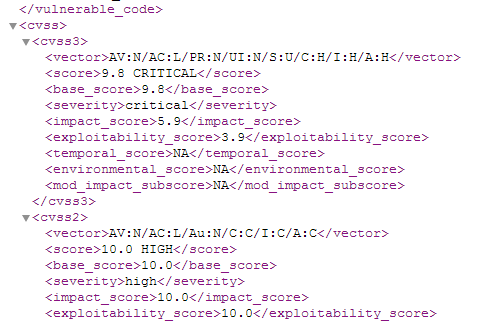
We're happy to announce that Syhunt version 6.3, released today, adds full support for CVSS. CVSS stands for Common Vulnerability Scoring System and is an industry open standard designed to convey vulnerability severity and help determine urgency and priority of response.
To enable the best use of the CVSS system, CVSS3 and CVSS2 vectors were assigned to all kinds of vulnerabilities currently detected by Syhunt Dynamic and Syhunt Code. Now, when a report is generated, vulnerabilities are sorted by default based on their CVSS3 score. This means that instead of the classic four-step sorting (High, Medium, Low, Info), there are now 101 possible vulnerability ratings, going from 0.0 (None) to 10.0 (Critical), determined during runtime. In addition to this, XML exports now contain full CVSS3 and CVSS2 data, such as the Base Score, Impact Score, Exploitability Score, Temporal Score and more.
| Rating | CVSS Score |
| None | 0.0 |
| Low | 0.1 - 3.9 |
| Medium | 4.0 - 6.9 |
| High | 7.0 - 8.9 |
| Critical | 9.0 - 10.0 |
Additional Improvements
- Added a Comparison report template that displays the evolution of vulnerabilities over time by automatically comparing previous scan session data related to a specific target.
- Added the ability to compare past scan sessions to determine new, unchanged or removed vulnerabilities, and save the comparison results as HTML (Menu -> Past Sessions -> Compare Checked button).
- Revamped PDF report generation.
Screenshots
We hope you enjoy the new release!
What's New in Syhunt 6.2 (June 15, 2018)

Syhunt now supports ASP.NET, Perl, PHP, Python, Java, JS and Lua code
It was only last month that we announced the addition of SAST (static application security testing) for Java to Syhunt, but good news, we have a new update to share today which brings SAST for Node.js based web applications. Syhunt 6.2 is able to scan the source code of Node.js web applications for security vulnerabilities with coverage for the Express and Koa frameworks. Because Syhunt was already able to dynamically test Node.js and MongoDB based web apps for vulnerabilities, this update makes Syhunt an ideal tool for both penetration testing and code review (DAST and SAST) of web apps built using the MEAN stack - MongoDB, Express.js, AngularJS & Node.js.
Code Checks for Node.js (Stable)
Syhunt 6.2 adds security code checks targeting Node.js web apps, covering:
- Cross-Site Scripting (XSS)
- SQL Injection
- Code Injection
- Unvalidated Redirect
- File Manipulation
- Command Execution
- HTTP Header Injection
- Log Forging
- Server-Side Request Forgery
- Input filtering/validation analysis
Note: Checks above in gray color are only available in the professional editions of Syhunt.
We hope you enjoy the new release!
What's New in Syhunt 6.1 (May 17, 2018)

Seven months later after the last big release of Syhunt, we're back with a significant update. Today we release version 6.1 of Syhunt Community and Hybrid. This version comes with the ability to scan the source code of Java EE and JSP web applications for security vulnerabilities, a long-awaited and much requested feature that makes Syhunt an ideal tool for both penetration testing and code review of Java apps (DAST and SAST).
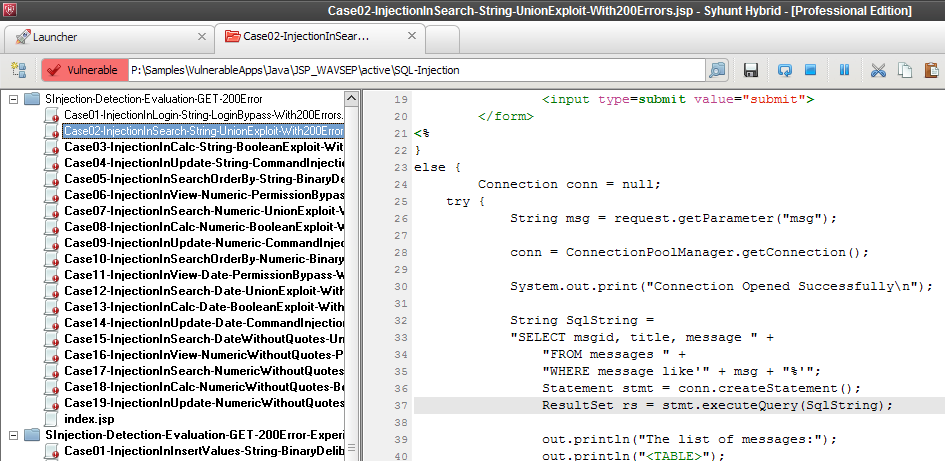
Ready to download and use
We comprehensively tested and reviewed the Syhunt 6.1 code scanner results with the help of over 1600 vulnerable Java web apps originated from the WAVSEP project, the NIST SAMATE project and Syhunt Lab's own test cases, reaching highly accurate detection rates of Cross-Site Scripting (XSS), SQL Injection, File Inclusion and many other security flaws. The full list of checks is available below.
Code Checks for Java (Stable)
Syhunt 6.1 adds 70 comprehensive security code checks targeting Java web apps, covering:
- Cross-Site Scripting (XSS)
- SQL Injection - including HQL
- Unvalidated Redirect
- File Manipulation
- Command Execution
- HTTP Header Injection
- LDAP Injection
- XML Injection (XXE)
- XPath Injection
- Log Forging
- Information Disclosure
- Input filtering/validation analysis
Note: Checks above in gray color are only available in the professional editions of Syhunt.
Code Checks for Lua (Beta)
Syhunt 6.1 brings support for an additional language: Lua, and is able to scan (though in beta form) the source code of Lua-based web applications compatible with Apache's mod_lua, CGILua and Lua Pages for vulnerabilities such as:
- Cross-Site Scripting (XSS)
- SQL Injection
- Local File Inclusion
- Command Execution
- Code Injection
- HTTP Header Injection
Other Improvements in Syhunt Code 6.1
- Improved XSS detection in multiple languages (classic ASP, ASP.NET & PSP).
- Improved input filtering analysis.
- Improved speed (scan optimization).
- Improved support for short write tag in multiple languages.
- Automatic Python WSGI script detection.
We hope you enjoy the new release!
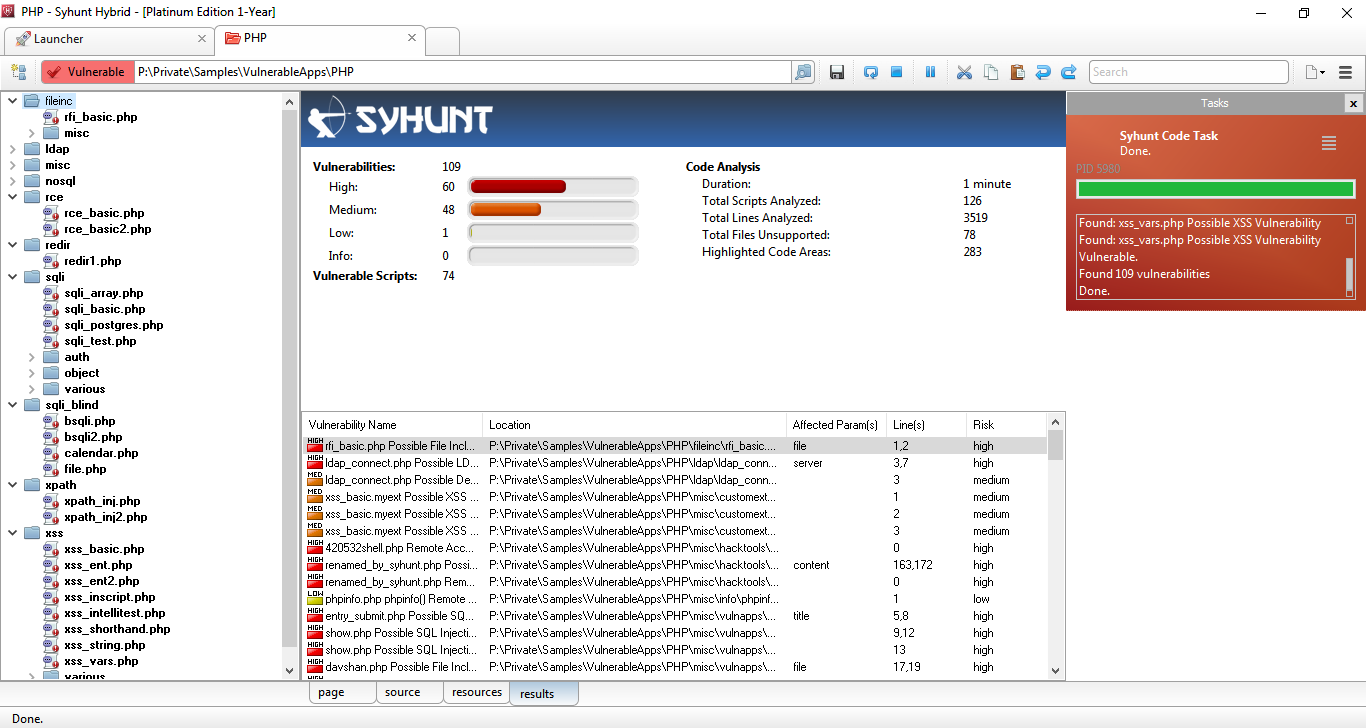
What's New in Syhunt 6.0 (October 10, 2017)
After a year of intense research and development, we're very proud to release version 6.0 of the Syhunt Hybrid application security testing suite. With its huge list of updates, the new version marks its most drastic evolution yet and a major overhaul of both its scan engine and user interface, adding advanced fingerprinting capabilities, enhanced spidering, injection, browsing and code scan capabilities, and a large number of new and improved checks.
Most of the improvements described on this page apply as well to the Community Edition of Syhunt released simultaneously today. If you prefer to read only what's new in Syhunt Community, visit here.
Revamped Hybrid User Interface
The new release adds the display of Hybrid, Dynamic and Code detailed scan statistics and progress both to the user interface and the command-line tools, and restores the site tree, implemented from scratch with the level of attention that it demanded.
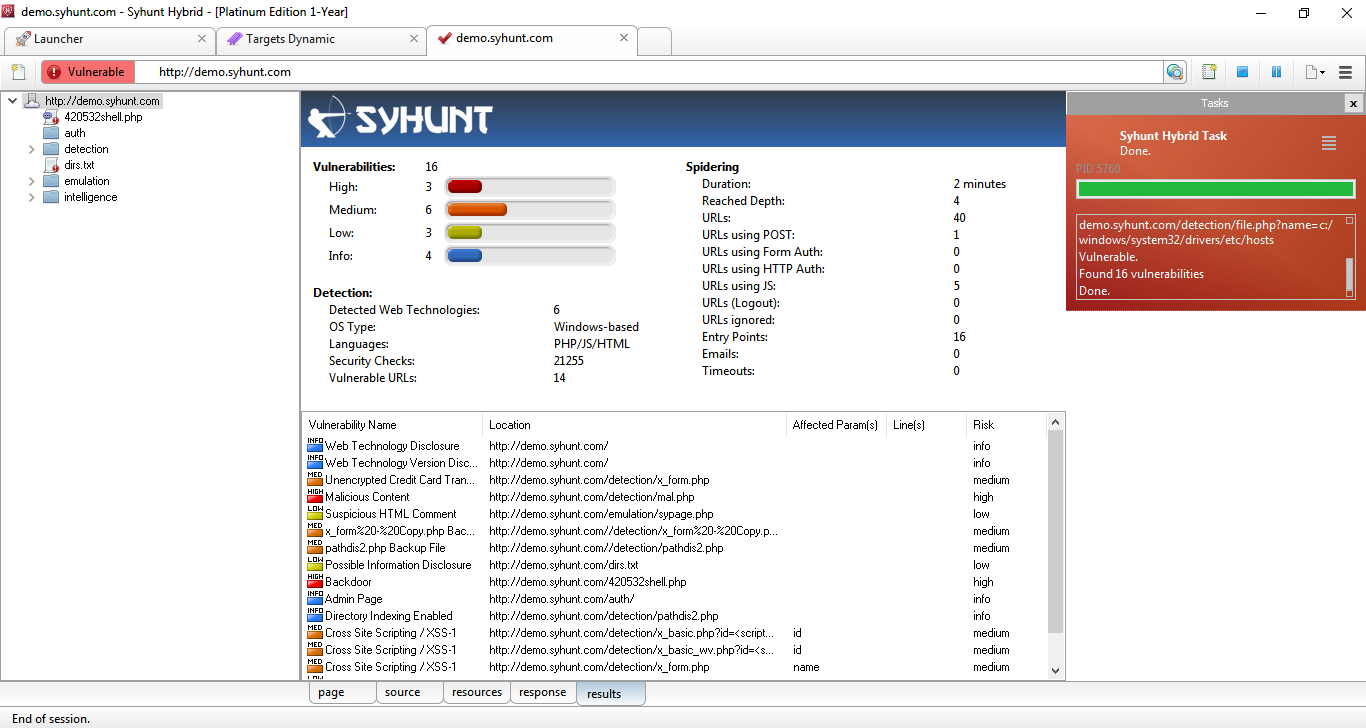
Syhunt Dynamic's UI while a demo scan is in progress
New Fingerprinting Capabilities
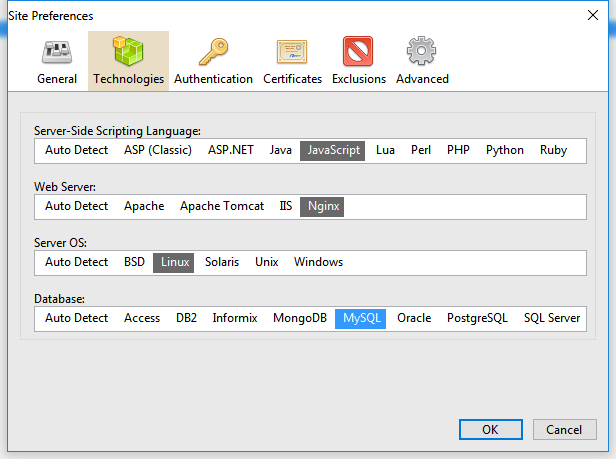
Because of the so many vulnerability checks and mutations added to this version, we developed an advanced and automated fingerprinter tightly integrated with the crawler that automatically maps all the web site technologies and optimizes a scan - this means that Syhunt Dynamic 6 checks are now executed based on the detected web technologies and platform, saving considerable time. The newly added Technologies tab part of the Site Preferences screen allows, if you prefer, to manually set the server-side scripting language, web server, OS and database for a target web site before starting a scan.
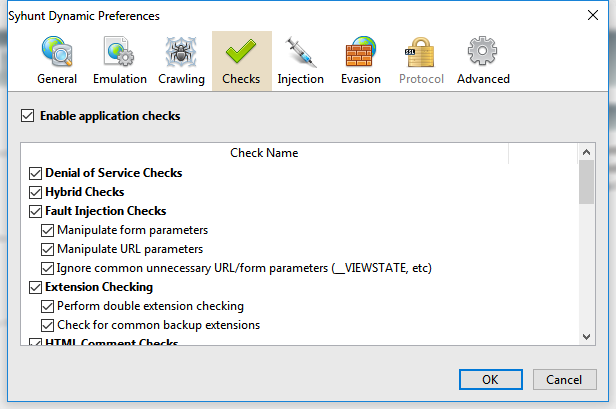
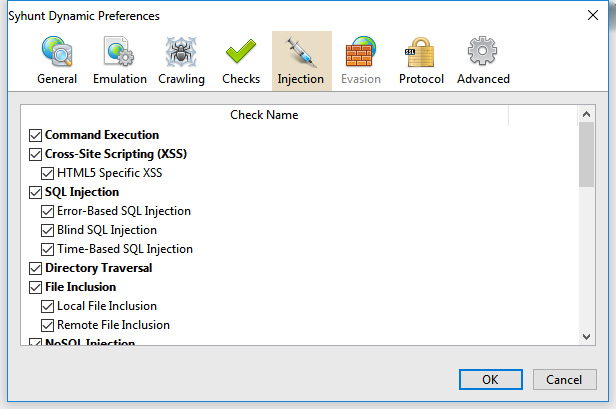
In addition to the changes above, the Checks screen has been revamped to accommodate a large number of newly added checks - you can find a list and details about the new checks at the end of this page as well as a link to the consolidated list of checks.
Four-Step Vulnerability Rating

This release comes with a four-step vulnerability rating (High, Medium, Low, Info). We added the Info risk classification and removed the Minimal risk classification. Vulnerabilities previously marked as Minimal risk were assigned a Low or Info risk depending on each case.
New Hunt Methods
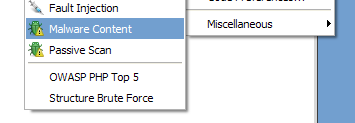
Malware Content - Added to both Syhunt Dynamic and Syhunt Code, allows to scan specifically for malware content, web backdoors, hidden debug parameters and signs of hacking.
Passive Scan - Added to Syhunt Dynamic, allows to scan specifically for Common Exposures, Source Disclosures, Web Technology Disclosures, Suspicious HTML Comments and Malicious Content within a website's surface.
Enhanced Dynamic Scanner
Several important enhancements were made to the spider which is a core part of Syhunt Dynamic:
- Faster and improved HTTP response analysis - improved parsing of web forms, JavaScript code and comments, and added support for additional HTML5 features.
- Added detection of known redundant app patterns.
- Added an option for enabling/disabling the use of Referer in HTTP requests (enabled by default).
- Improved file format and relative path handling.
- Improved cookie and token handling.
- Improved auto form filling, auto login and logout detection (many additional cases covered).
- Improved page redirect handling.
Enhanced Code Scanner
- Significantly faster scans (revised code for scan optimization)
- Improved entry point mapping - Added detection of new entry points in PHP code, allowing additional vulnerability cases to be detected.
- Added automatic file format detection.
- Improved reporting of vulnerable lines
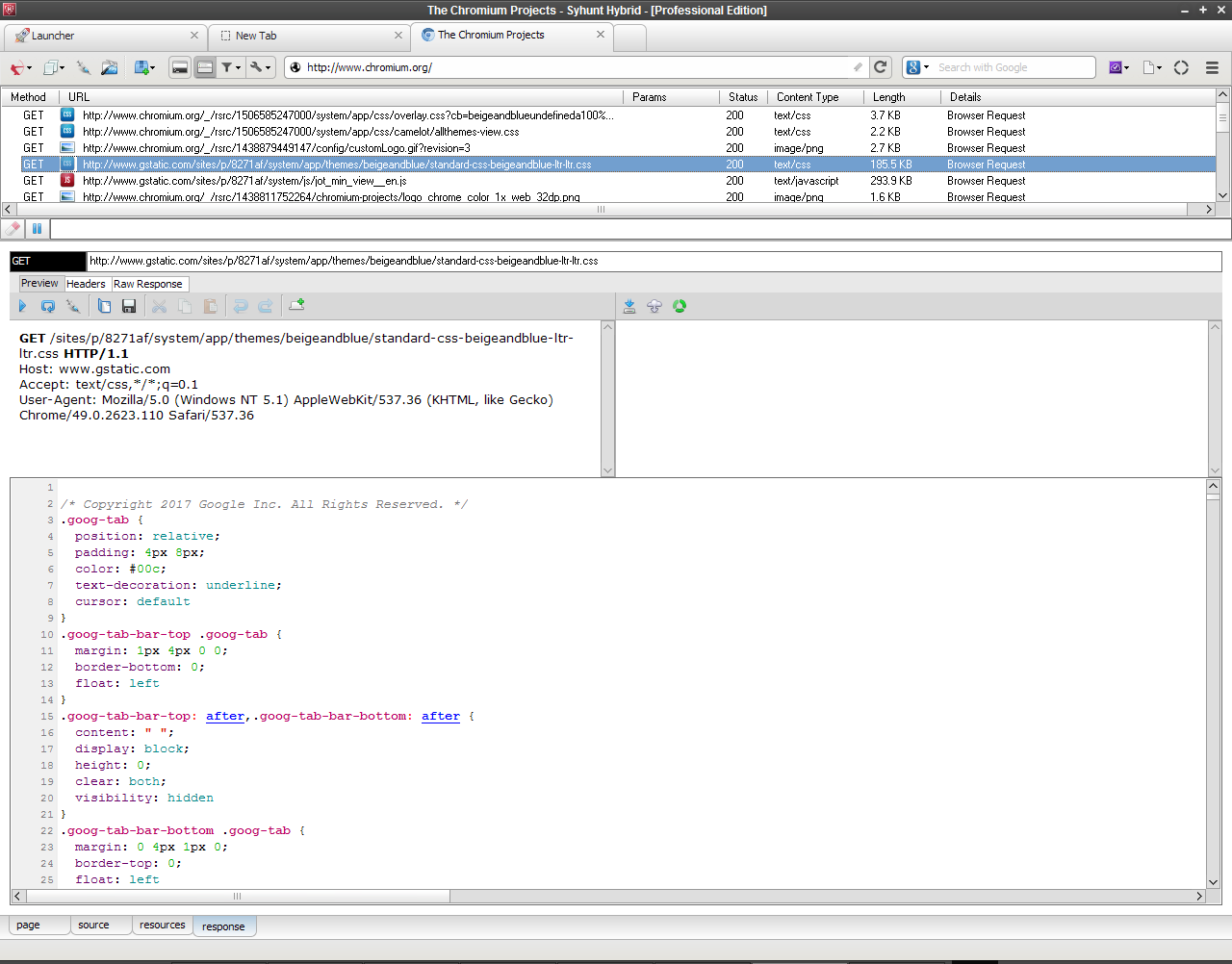
Enhanced Web Browser (Sandcat 6)
- Request Viewer rewrite with better display of requests and important stability fixes
- Simplified the tabbed UI - Major tab code clean up and reorganization.
- Disabled the Chromium's XSS protection - especially useful for performing manual testing or manually confirming XSS detection cases.
New Dynamic Checks
Added detection of many additional vulnerability classes through dynamic application security testing:
- Code Injection in multiple languages - ASP Classic, ASP.NET, Java/JSP, Lua, Perl, PHP, Python, Ruby & Server-Side JavaScript are covered, using both print-based and time-based detection techniques and taking in consideration different web server environments. CWE-94
- Expression Language (EL) Injection in JSP web applications - CWE-917
- XML Injection and XML External Entity (XXE) Injection - CWE-661 and CWE-827
- Authentication Bypass vulnerabilities - CWE-287
- Authentication Brute Force - Both form and HTTP-based, fully automated with common weak passwords
- Debug Parameter Discovery and Injection
- Malicious Content Detection
- Innappropriate Content Detection - Like adult or warez content
- Web Technology Disclosures - Reports if the version of a detected web technology is being disclosed.
Improved the detection of several vulnerability classes:
- SQL Injection - Added additional checks for error-based and time-based SQL Injection, and improved checks for MySQL, MS SQL and PostgreSQL
- NoSQL Injection - Added MongoDB error-based detection
- Remote Command Execution checks - Added time-based detection and new variants
- Directory Traversal checks - Added many new variants and filter evasion techniques
- Cross-Site Scripting (XSS) - Added a subcategory for Client-Side Denial-of-Service
- Web Backdoors - Added 211 new known backdoor checks
- File Inclusion - Added many new variants and improved detection
- Source Code Disclosure - Added new variants covering server-side Lua, PHP and ASP code, and improved accuracy
- LDAP Injection checks - Improved detection
- CRLF Header Injection checks - Added new variants and improved confirmation
- Server-Side Includes Injection checks - Added new variants
- XPath Injection checks - Added new variants and improved confirmation
- HTML Comment checks - Introduced a more advanced parser, added support for JS comments, added several new checks and eliminated false positive cases.
- Backup File Checks - Eliminated a common false positive case.
- Structure Brute Force Checks - Extended many checks to cover web root, added normal and paranoid modes, checks for admin pages now performed as part of the brute force checks.
- Vulnerable Web Apps - Revised checks for known vulnerable web apps divided into multiple categories: Apache Struts, ASP, ASP.Net, Flash, Dynamic HTML, Java, Perl, Python, Ruby, ColdFusion, SSI, IIS...
- Multiple Disclosure checks - Revised checks for multiple disclosure flaws (divided into Path Disclosure, Password Disclosure, Database Disclosure and Information Disclosure). Fixed a case that could result in duplicated Path Disclosure reporting.
- Common Form Weaknesses - Improved checks for multiple form input related vulnerabilities, such as Unencrypted Login, Email Form Hijacking, Hidden Price Form Field and AutoComplete Enabled in sensitive form inputs.
- Common Exposures, Suspicious HTML Comments and Directory Listing checks - Introduced a new, extended check database and eliminated some possibilities of redundant reporting.
New Code Checks
Added detection of many not previously covered vulnerabilities through static application security testing:
- XPath Injection vulnerabilities - CWE-643
- LDAP Injection vulnerabilities in PHP code - CWE-90
- SQL Injection involving object-oriented PHP code
- Web Backdoors in source code
- Debug Parameters
- Common Form Weaknesses
Improved the detection of the following checks:
- Arbitrary File Manipulation checks - Added new PHP variants
- Weak Password Hashing check - Revised and fixed false positive cases
Other Improvements and Bug Fixes
- Added detection of new hacking tools through web server log analysis (Syhunt Insight).
- Scan status now reported as Undetermined if the scan aborted before starting due to any serious connectivity issues (like host not found).
- Re-implemented WAF/IDS evasion and detection in Syhunt Dynamic.
- Fixed: short hunt method options (like as for appscan) not working with the newly introduced CLI app ScanURL.exe. Made it print additional vulnerability details.
- Fixed: location URL in reports including manipulated POST params
We hope you enjoy the new release!
