What's New in Syhunt 7.0.12
April 1, 2024
Syhunt Hybrid 7.0.12 adds OWASP Top 10 Mobile 2024
Syhunt Hybrid now checks for the 2024 OWASP Top 10 Mobile Risks in both Android and iOS applications.
Syhunt is thrilled to announce the integration of the OWASP Top 10 Mobile 2024 risks list into our premier application security scanner, included with Syhunt Hybrid version 7.0.12. This strategic update signifies our commitment to staying at the forefront of cybersecurity defenses, enabling our clients to more effectively identify and mitigate the most critical security threats facing mobile applications today. By incorporating the latest insights and recommendations from globally recognized lists, Syhunt continues to enhance its MAST capabilities, ensuring that our users are equipped with the most advanced tools to protect their mobile applications against emerging security vulnerabilities and threats. Our primary aim is to empower developers to detect and fix vulnerabilities proactively, before publishing their applications.
Building on our tradition of excellence in application security, Syhunt recently extended its support to include the CWE Top 25 2023 list of the Most Dangerous Software Errors, marking a significant enhancement in our scanner's ability to uncover and help address critical vulnerabilities across a wide range of applications. This development, coupled with the introduction of SAST capabilities for mobile applications developed in Kotlin and Delphi XE, complements our existing support for Java, Swift, and Objective-C. These advancements not only broaden the scope of our security solutions but also underscore Syhunt's dedication to adapting to the evolving technological landscape and the diverse needs of our clients, ensuring they are equipped with a comprehensive toolkit to safeguard their applications against the most pressing security challenges.
The OWASP Top 10 Mobile Risks
Syhunt's latest update encompasses a comprehensive defense mechanism against a spectrum of mobile application risks, as outlined by the OWASP Top 10 Mobile 2024 list. This includes safeguarding the following risks:
| M1: Improper Credential Usage |
| M2: Inadequate Supply Chain Security |
| M3: Insecure Authentication/Authorization |
| M4: Insufficient Input/Output Validation |
| M5: Insecure Communication |
| M6: Inadequate Privacy Controls |
| M7: Insufficient Binary Protections |
| M8: Security Misconfiguration |
| M9: Insecure Data Storage |
| M10: Insufficient Cryptography |
Additional Improvements in 7.0.12
- Added support for OWASP Top 10 Mobile 2024 scan in scan scheduler.
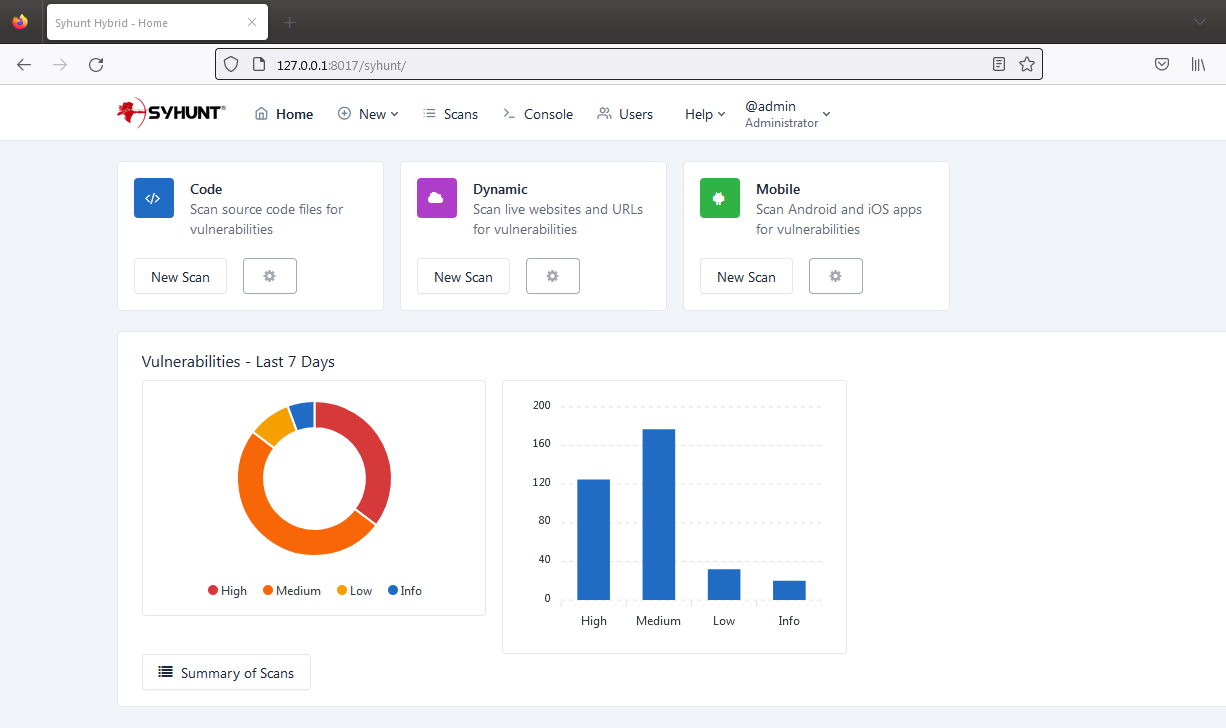
- Added Syhunt Mobile to the web UI dashboard - only available if the existing license includes it.
- Added the ability to disable accounts in the web UI (requires admin privilege)
- Improved multi-user support in web UI. Please note that, due to a change in how account settings are stored, after upgrading you will be asked to reset your account passwords.
- Added -langset parameter to scancore command that allows to set the default web UI language. This applies to the login screen as well.
- Migrated AI model for patch generation.
- Improved JSON parsing.
That's all, for now. Happy bug hunting!