What's New in Syhunt 6.7
September 17, 2019



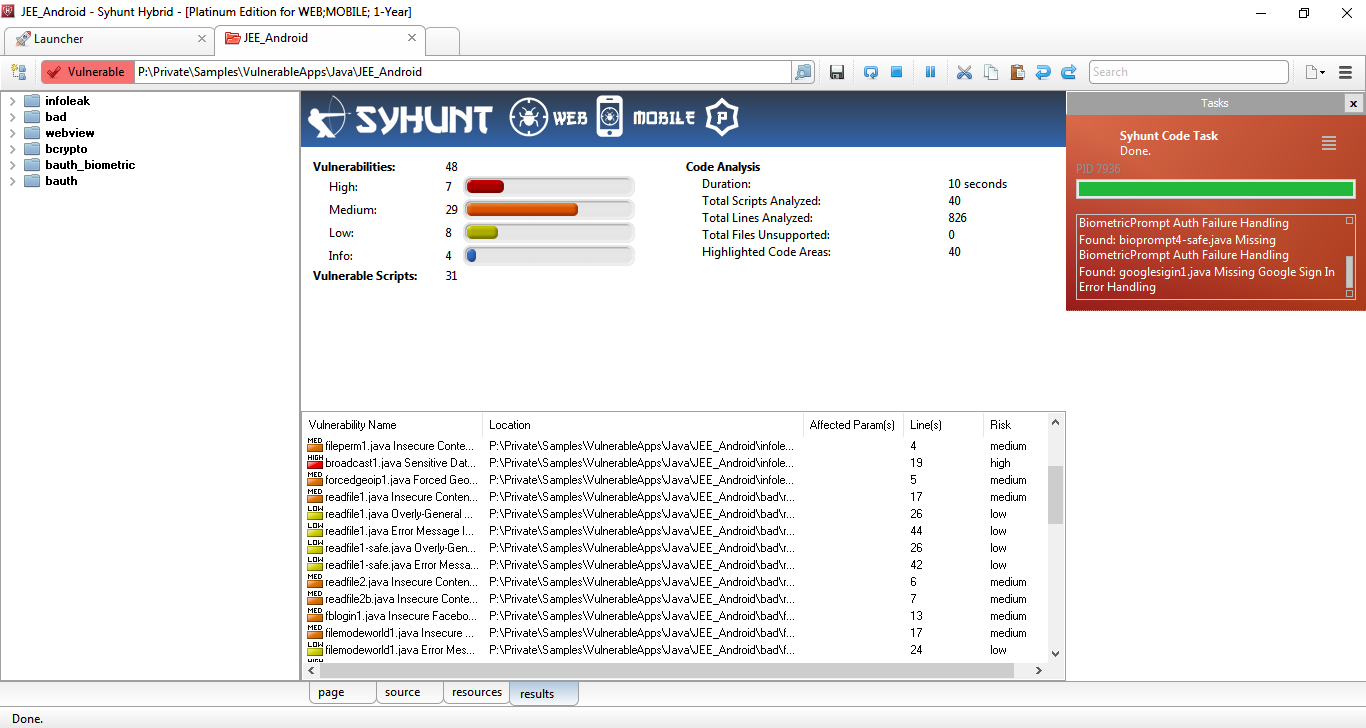
Syhunt adds support for Android and iOS apps and greatly extended checks for Java
We're excited to announce the immediate availability of Syhunt version 6.7. This release is a milestone in Syhunt's development history. It brings support for mobile (Android & iOS) applications, greatly extends its Java check base and adds the much-awaited scan scheduling feature. As part of this major update, we've added checks and support for the Swift and Objective-C programming languages, which are the primary languages used for iOS app development, and increased the number of source code checks for Java, the primary language used for Android app development, from 70 to 310 checks. The newly added features and checks, together with Syhunt's ability to scan JavaScript-based applications, including Angular and Node.js, make Syhunt suited for both mobile and web application security assessment. The new release also introduces a Mobile Compliance report template which focuses on the OWASP Mobile Top 10 risks list, as well as the CWE/SANS Top 25 Most Dangerous Software Errors and the PCI DSS v3,2.1 standard.
With this update, users of the Community edition of Syhunt will be happy to know that they can now perform a near-complete source code scan, as all code checks are now included with Syhunt Community, though the details of High-rated and specific Medium-rated vulnerabilities are only available in the professional editions of Syhunt.
The mobile support is available in limited preview in Syhunt Community and fully available to new and existing customers through a separately licensed product extension known as Syhunt Mobile. The newly added Java checks for web applications are available to existing customers at no additional cost.
New Code Checks for Java
Syhunt 6.7 adds security code checks targeting Java-based web and mobile apps, covering:
- Code Injection (CWE-94)
- Insecure Communication
- Insecure Cryptographic Algorithms (CWE-327)
- Regular Expression Injection (CWE-400)
- SQL Injection (Spring Framework)
- Uncontrolled Format String (CWE-134)
- Various bad practices
Improved and extended checks for Java include: Broken Authentication, Broken Cryptography, Security Misconfiguration, Cross-Site Scripting (XSS), Command Execution, Code Injection, File Inclusion and Manipulation, SQL Injection, LDAP Injection, XML Injection, Information Leakage, Log Forging and Denial-of-Service.
Code Checks for Swift & Objective-C
Syhunt 6.7 adds security code checks targeting the primary iOS development languages, covering:
- Broken Authentication
- Command Execution
- Insecure Communication
- Insecure Data Storage
- Insecure Hashing Algorithm
- Insecure Cryptographic Algorithms
- Uncontrolled Format String
- Hardcoded Sensitive Information
- Buffer Overflow
- Various bad practices
Other Code Improvements
- Improved vulnerability detection accuracy and vulnerable line detection precision.
- Improved insecure randomness checks (additional checks).
- Improved multi-language source code parsing.
- Additional entry point coverage and input filtering/validation analysis.
Dynamic and Other Improvements
- Improved automated web form login (alternative schemes).
- Improved spidering of heavily dynamically generated web stores.
- Minor optimizations for Wordpress-based websites.
- Added a built-in Scan Scheduler. For detailed information, see: Scheduling Scans
- Allow to ignore specific vulnerabilities in Site Preferences and Code Scanner Preferences screen.
- Improved session status and icons in session manager.
- Fixed: a few bugs and false positives (as detailed in the CHANGELOG)
We hope you enjoy the new release!
