Syhunt's whitebox scan (source code scan) can uncover multiple classes of application vulnerabilities and also identify key areas of the code that need review. Its static source code analysis functionality can detect cross-site scripting, file inclusion, SQL injection, command execution and validation problems. Initially only PHP was supported. As of 2011, multiple web programming languages are supported.
Important: If you specify a hunt method other than Source Code Scan (codescan) you will be performing a gray or black box test and remote connections will be made. Read the Black Box or Gray Box guides for details on how to perform them.
Via the Syhunt Suite UI
- Launch Syhunt.
- Configure any custom source code extensions, if required (you can do this under menu Advanced|Scan Settings -> Source tab). For example: if you have PHP scripts with a .foo extension, add ".foo=.php".
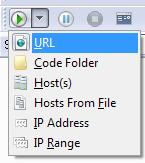
- Press the Scan button
 in the toolbar and select Code Folder as target type.
in the toolbar and select Code Folder as target type.
- Assign a target source code folder.
- Select Source Code Scan as Hunt Method
- Press the OK button.
Via SyMiniCS
- Go to the directory Syhunt Suite is installed using the command prompt.
- Example command-line:
SyMiniCS.exe localhost -sn:Scan1 -hm:codescan -srcdir:"C:\WWW\Docs\" -gr
Note: you still need to specify a target host, but no remote connections will be open.
Via Session Launcher
Session Launcher doesn't support white-box testing. It can perform a hybrid scan though. Read the Gray Box guide for more details.