Syhunt's unique gray box/hybrid scanning capability allows it to scan the application's source code first, acquire important information about them, and then try to remotely confirm flaws (XSS, File Inclusion, SQL Injection, Command Execution, etc) by using this information.
How to perform a gray box testing
Performing a gray box testing with Syhunt is very easy:
- First, click the Scan button
 in the toolbar.
in the toolbar.
- Choose an appropriate Hunt Method listed as of graybox type.
- Assign the Start URL and the source code directory. The source code directory must contain a copy of the web site source files. Now this is very important: When assigning a source code directory, you must point exactly to the root of the web site (where the index files are located).
- Hit OK
This is often everything you need to perform a gray box testing, see below the details about each step.
Via the Syhunt Suite UI
- Launch Syhunt.
- Configure any custom source code extensions, if required (you can do this under menu Advanced|Scan Settings -> Source tab). For example: if you have PHP scripts with a .foo extension, add ".foo=.php".
- Click the Scan button
 in the toolbar and select a target type.
in the toolbar and select a target type. 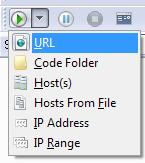
- StartURL and IP Address allow you to assign a single target and the site source code directory
- Host(s), Load from file, IP Address and IP Range allow you to assign multiple target hosts. You can assign a source code folder to each target host using the Hosts sidebar (see below).
- Code Folder allow you to quickly assign a target source code folder. The target host is automatically changed to localhost (127.0.0.1) when this option is selected.
- Select the appropriate Hunt Method.
- Press the OK button.
Making the Source Code Folder a permanent setting
You can assign a source code folder to specific targets using the Hosts sidebar.
- Switch to the Hosts sidebar.
- Select or enter the desired target host in the sidebar
- Assign the site source code directory in the General tab.
Via SyMiniCS
- Go to the directory Syhunt Suite is installed using the command prompt.
- Use the following command-line:
SyMiniCS.exe [targethost] -sn:[a sessionname] -hm:[a huntmethod]] -srcdir:"[SourceDir]" -gr Example: SyMiniCS.exe localhost -sn:Example -hm:complete -srcdir:"C:\WWW\Docs\" -gr
Note: if you already entered the source code directory for the target host using the Syhunt Suite GUI in a past scan it is not necessary to assign it again using the -srcdir command. If needed, you can quickly change the source directory stored in the Syhunt Suite installation settings by calling:
SySuite.exe -edtrg -hosts:[hosts] -ports:[ports] Example: SySuite.exe -edtrg -hosts:127.0.0.1 -ports:80
Generating reports
SyMiniCS reports are automatically generated and saved if the -gr parameter is provided.
You can also open the session with the main Syhunt Suite UI by calling:
SySuite.exe -s:[session name]
Or by launching Syhunt Suite, and using the menu File -> Load session... option.
Via Session Launcher
- Launch Seslaunch.exe
- Click menu File -> New Session
- In the Create New Session dialog, enter the target hosts
- Click the Target Settings link.
- In the Target Settings screen, select the target host in the sidebar
- Click Target Settings in the tree, then check Enabled
- Click Source in the tree, then assign the site source code directory
- Close the Target Settings screen.
- Select the appropriate Hunt Method.
- Press OK.
Hybrid Scanning - How It Works (PHP Examples)
Syhunt is able to detect vulnerabilities in the source code files (locally) and live (remotely). When it does both, it is called gray box or hybrid scanning.
Imagine you have the following code online at http://yourhost/index.php and you don't know it is vulnerable:
<? $n = $_POST['name']; ?> <html> <body> <form method="POST" action="index.php" name=f> <input type="text" name="name"> </form> <? echo $n; // XSS (POST) ?> </body> </html>
And locally in the "C:\Www" directory you have this copy of the source code of the page. You start your scan with the following command:
SyMiniCS yourhost -hm:xss -srcdir:"C:\Www\"
Syhunt scan results will be:
In /index.php (source code, locally), affecting parameter "name", on lines 1,7: Possible XSS Vulnerability In /index.php (live, remotely), affecting parameter "name": Confirmed XSS
As you can see, it not only detected the vulnerability locally (in the source file), but also detected it online by connecting to the host, parsing the HTML, detecting the form input and then simulating injection attacks.
Hidden Parameter Scanning
Let's look at a slightly different example of vulnerable code:
<? $m = $_GET['msgtouser']; // Hidden ?> <html> <body> <? echo $m; ?> </body> </html>
What would happen if this was online? You would not be able to tell by merely visiting the page that it is vulnerable. Again you start your scan with the following command:
SyMiniCS yourhost -hm:xss -srcdir:"C:\Www\"
Syhunt scan results will be:
In /index.php (source code, locally), affecting parameter "msgtouser", on lines 1,4: Possible XSS Vulnerability In /index.php (live, remotely), affecting parameter "msgtouser": Confirmed XSS
This time, by examining the code, Syhunt learned about the hidden "msgtouser" parameter, used it later when simulating injection attacks and was able to confirm the vulnerability online.